European electricity infrastructure has become a target of sustained hybrid warfare, and a new report from Eurelectric, the region’s power sector trade group, finds that most of the continent’s utilities are not prepared for it.
In a February 2026 report, Battle-Tested Power Systems: Resilience and Preparedness for Europe’s Electricity Sector, Eurelectric documented an accelerating campaign of physical sabotage, cyberattacks, aerial intrusions, and subsea cable severances targeting energy assets across the European Union (EU). The findings arrive as European defense planners warn that Russia could move against North Atlantic Treaty Organization (NATO) allies as early as 2028, and as conflicts in the Middle East have shown, again, how quickly modern warfare destroys electricity infrastructure. In Europe, the timeline compresses the runway for utilities, regulators, and policymakers to act, the report warns.
“As the war approaches its fourth year,” it says, “the strategy remains central to Russia’s war effort, and the Sisyphean challenge of powering Ukrainian society during that time provides important insights for the rest of Europe on best practices to protect electricity infrastructure from attack.”
The numbers are already staggering. Armed Conflict Location & Event Data (ACLED), an independent non-profit organization that claims to be “the world’s most trusted source for real-time data and analysis on political violence and protest,” tallied 1,065 attacks on Ukrainian energy infrastructure through the end of 2024 in its Ukraine Conflict Monitor. World Bank damage estimates exceed $20 billion, the report says, even though it notes that precise attack figures remain incomplete in public records for security reasons. “This nonetheless implies that the data presented above are only the tip of a larger iceberg,” the report says.
In 2025 alone, Ukraine sustained 1,225 attacks, which overshadowed the cumulative total of the prior three years. The bulk of the attacks were notably concentrated in the final four months. On Nov. 8, 2025, for example, a single strike deploying 450 exploding bomber drones and 45 missiles hit 25 locations simultaneously, cutting power across five regions. It was timed to maximize civilian exposure ahead of winter in a deliberate deployment of what it calls “General Winter,” the report says.
Sabotage and Cyberattacks Expose Europe’s Grid Vulnerabilities
Europe’s grid has also taken direct hits, particularly on the Baltic Sea floor, which has become contested infrastructure. In November 2024, the Chinese-flagged Yi Peng 3 is suspected of dragging its anchor across two subsea data cable routes in the same transit—severing the C-Lion1 fiber-optic link between Finland and Germany and the Arelion communications cable between Sweden and Lithuania. Six weeks later, on Christmas Day, the Eagle S—a cargo vessel registered in the Cook Islands (a South Pacific flag of convenience jurisdiction favored by operators seeking to obscure ownership and dodge sanctions)—cut the Estlink-2 power cable in the Gulf of Finland. While Estonian authorities pegged the repair bill at up to €60 million, Eurelectric noted the figure covered neither the lost transmission capacity nor necessary security measures spearheaded by NATO’s Baltic Sentry mission, which was tasked in January 2025 to specifically patrol the sea lanes. While aerial incursions over Poland, Romania, and Estonia in September 2025—including Russian fighter jets holding position in Estonian airspace for 12 minutes before NATO escorts arrived—did not cause direct damage to power infrastructure, they highlighted more crucial vulnerabilities.
And beyond physical attacks, London-based geopolitical and security intelligence firm Dragonfly Intelligence tallied 23 successful cyberattacks on Europe’s energy sector from the start of the war in Ukraine to October 2024 alone. On the first day of Russia’s 2022 invasion, a suspected Russian cyberattack disabled remote monitoring via satellite for 5,800 German wind turbines—representing 11 GW of capacity across operators including Enercon, one of Europe’s largest turbine manufacturers.
Sandworm, a unit of Russia’s military intelligence agency (GRU), is suspected in the most extensive cyberattack Denmark has ever experienced—a May 2023 campaign that compromised 22 energy companies by exploiting vulnerabilities in Zyxel firewalls, including zero-days in the second attack wave, forcing affected operators into island mode. Attribution, however, remains disputed.
Between Dec. 29 and Dec. 30, 2025, hackers penetrated Polish energy infrastructure, gaining access to combined heat and power plants, and renewable generation management systems, though the attack was successfully defended, avoiding a blackout. Perhaps more concerning is that in April 2025, hackers exploited a weak password in an industrial control system to open the water valve at Norway’s Lake Risevatnet dam to full capacity. The reservoir drained, and while the physical damage was limited, “The uncertainty such actions sow is an arguably more valuable outcome than any real damage caused,” the report says.
“The geopolitical picture has developed,” Markus Rauramo, Eurelectric’s president, said ahead of the report’s release. “Now there are more scenarios that we ought to take seriously and prepare for. For me it is not either/or. These are on a sliding scale—from the traditional risk of asset unavailability or grid instability to low probability but high impact potential of hybrid or cyber or even kinetic, with hostile actors trying to impact our availability.”
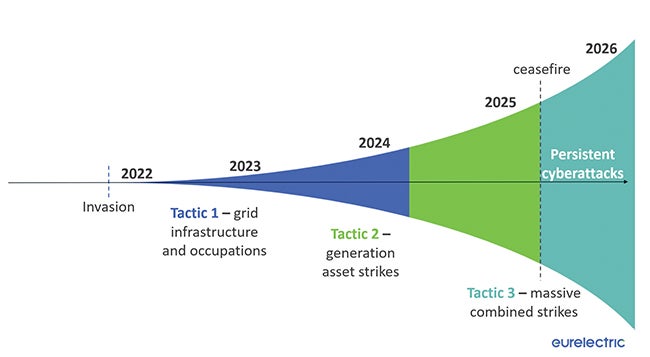 |
| 1. Russia’s attack tactics against Ukraine’s energy infrastructure have evolved through three distinct phases since the February 2022 invasion, spanning grid disconnection and occupation, to targeted generation asset strikes, to the massive combined drone-and-missile barrages that have dominated since late 2024. Cyberattacks have persisted across all three phases. Courtesy: Eurelectric, Battle-Tested Power Systems, February 2026. |
Eurelectric’s analysis suggests Russia’s tactics evolved through three distinct phases (Figure 1). Artillery shelling gave way to drone and missile warfare, including Iranian-made Shahed drones—low-cost, GPS-guided one-way attack aircraft that detonate on impact, which Russia now mass-produces domestically under the designation Geran-2—and increasingly precise “double-tap” strikes. These are drones launched in volume to breach physical fortifications, followed by precision missiles to destroy the equipment behind them.
During the Ukraine War, initial focus on transmission substations shifted to centralized generation assets once Ukraine demonstrated it could reconnect a fragmented grid, the report says. By September 2023, more than 6,500 missiles and 3,500 drones had destroyed approximately 50% of Ukraine’s energy infrastructure and more than 67% of its thermal generation capacity, according to the Centre for Global Studies. The most recent phase, since September 2025, has been the most destructive. “The sheer number of munitions used means even with a 60–70% shoot-down rate, the few that get through remain fatal,” DTEK told Eurelectric.
The two most targeted assets, notably, have been gas compressors and primary electrical transformers, which are likely chosen for their system-critical role and long procurement lead times. Cyberattacks, meanwhile, have occurred constantly throughout all three phases, increasing 30% to 40% since the invasion began, according to DTEK, and are now accelerating given an artificial intelligence-driven arms race between Russian offensive models and Ukrainian defensive systems.
Significantly, the report draws a clear operational boundary between military defense of assets, which is the state’s responsibility, and preparedness, which is the utility’s. “The onus nonetheless falls on power companies to practice effective preparedness,” it says, “centering around three phases: preparation, response and recovery.”
“I would focus on three points: situational awareness—understanding the geopolitical picture and the threat picture you are facing,” Rauramo said. “Then have good authority contacts, so have a two-way communication continuously. And then exercise. You become a master by practicing and exercising.” Resilience Under Fire: How Ukraine’s Energy Sector Is Adapting—and What It Means for Europe, a June 2025 analysis of infrastructure attacks, published by advisory firm Rasmussen Global, analyzed Russia’s attack patterns in Ukraine and identified physical hardening measures, he noted. “What we can take from that report is what a hostile actor is targeting and what kind of damage and disruption is inflicted on potentially our assets—and then actually play that back to our situation. What kind of stockpile should we have? What kind of spares are in this critical infrastructure? And then think even further about lead times and availability of the parts that could be impacted.”
Physical hardening, which could include gabions, sandbags, concrete shielding, and drone nets, is the cheapest and most widely deployed form of protection, the Eurelectric report says. The cost calculus points to critical nodes: a nodal substation aggregating hundreds of megawatts is a more defensible investment than individual turbines, it argues. Transformer stockpiles will also be essential, though their locations must be kept secret and decentralized. Notably, Ukraine’s energy ministry pioneered a “Mobile Brigade” to recover usable equipment from decommissioned assets across Europe—a procurement template the report recommends to European operators.
DTEK’s response has also been instructive. Anticipating the capture of one of its thermal power plants, the utility disassembled the entire facility before the final attack, retrofitting recovered equipment into other plants still operating. That approach “can sometimes be more pragmatic to repair equipment, rather than prevent damage with expensive asset fortifications,” the report says.
Ukraine’s recovery has meanwhile relied heavily on its national energy and climate plan, which targets a 27% distributed energy resource share by 2030, treating decentralization as a security imperative. DTEK opened 200 MW of battery storage in September 2025, deliberately spread across six sites to reduce the impact of any single strike, using batteries supplied by Fluence. “In the EU, we cannot afford to wait and see,” the report concludes.
EU Directives and NATO Spending Drive Push for Grid Hardening
In the EU, so far, the legislative framework appears substantive. The Critical Entities Resilience (CER) Directive, the Network and Information Security Directive 2 (NIS2), and the Electricity Market Design Reform collectively mandate risk assessment, physical site protection, operational technology (OT)-information technology (IT) cybersecurity segmentation, and shock-absorption capabilities. The problem is clearly delivery: While CER required national transposition by October 2024, numerous member states missed that deadline. “Progress across Europe’s power sector remains a patchwork of different levels of preparedness, with TSOs [transmission system operators] and DSOs [distribution system operators] respecting different levels of guidance depending on their country,” the report says.
The urgency for action, however, remains considerable. Eurelectric’s benchmark survey asked European utilities to rate their own preparedness for hybrid threats and crisis scenarios on a 10-point scale, where 1 meant preparedness was not considered at all and 10 meant readiness for any crisis that could occur. Responses averaged 6.7. And yet, the report is explicit that this overstates the reality, given that only the more preparedness-conscious utilities chose to participate.
As outliers, Nordic and Baltic operators treat hybrid risk as an operational reality, it says. Finland’s Total Defense model, coordinated through the National Emergency Supply Agency (NESA), embeds Fingrid—the Finnish TSO—directly into national defense planning through joint exercises, classified briefings, and compulsory stockpile oversight. Still, contact between utilities and national authorities across the broader sector is largely informal and flows in one direction. “This dependence on informal channels and a lack of two-way information sharing highlights a structural weakness,” the report says.
On financing, Rauramo was direct. “In order to really prepare, you need to reinforce your critical infrastructure—transformer stations, critical power plants. You need to build underground operating rooms. You need personal protective equipment, sandbags, plywood. This is certainly already defense-related spending.” Awareness is critical, he suggested. “We certainly as a critical infrastructure provider can point to the authorities that this could be part of the 1.5% spending for NATO compliance.”
NATO-allied countries have agreed to raise defense spending to 5% of gross domestic product (GDP), of which 1.5 percentage points are earmarked for critical infrastructure protection and cybersecurity. For now, Eurelectric estimates the pool at approximately €250 billion. However, the governance mechanism to direct that capital specifically to grid hardening does not yet exist. On shared responsibility, Rauramo offered the Nordic model as a template. “When everybody chips in a little bit, we get big impact. We cannot rely on one party taking the whole responsibility.”
—Sonal Patel is senior editor at POWER magazine (@sonalcpatel, @POWERmagazine).