For the first time ever, the U.S. has filed criminal charges against known state actors for hacking U.S. interests. A grand jury in the Western District of Pennsylvania indicted five Chinese military hackers for computer hacking, economic espionage, and other offenses directed at six American victims in the U.S. nuclear power, metals, and solar products industries over the period 2006 to 2014.
The U.S. Department of Justice (DOJ) May 19 announcement of the 31 counts alleges that the “defendants conspired to hack into American entities, to maintain unauthorized access to their computers and to steal information from those entities that would be useful to their competitors in China, including state-owned enterprises (SOEs). In some cases, it alleges, the conspirators stole trade secrets that would have been particularly beneficial to Chinese companies at the time they were stolen. In other cases, it alleges, the conspirators also stole sensitive, internal communications that would provide a competitor, or an adversary in litigation, with insight into the strategy and vulnerabilities of the American entity.”
The named victims were Westinghouse Electric Co., U.S. subsidiaries of SolarWorld AG, United States Steel Corp., Allegheny Technologies Inc., the United Steel, Paper and Forestry, Rubber, Manufacturing, Energy, Allied Industrial and Service Workers International Union, and Alcoa Inc.
China denied the charges the following day.
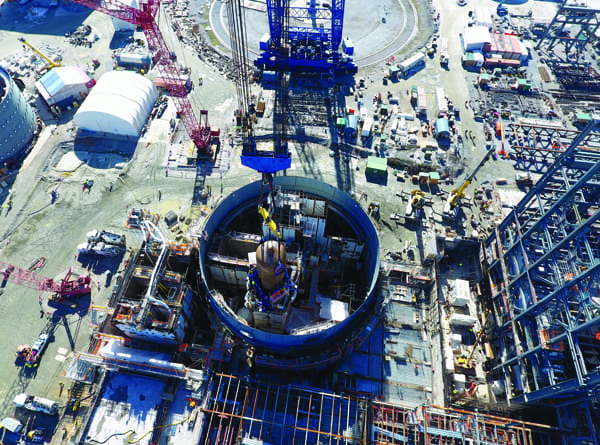
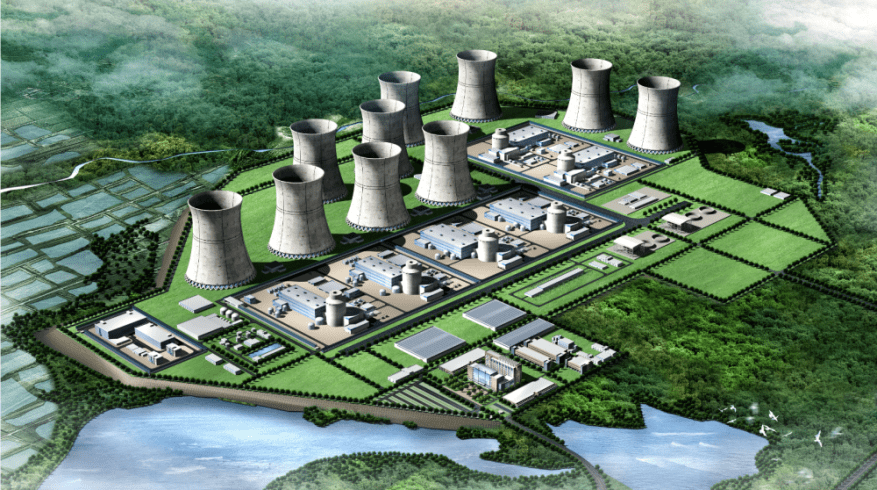
The criminal conduct involving Westinghouse included activities in 2010 and 2011. In 2010, while Westinghouse was building four AP1000 power plants in China and negotiating other terms of the construction with a Chinese SOE, including technology transfers, the indictment alleges that one of the defendants stole confidential and proprietary technical and design specifications for pipes, pipe supports, and pipe routing within the AP1000 plant buildings. In 2010 and 2011, while Westinghouse was exploring other business ventures with SOE-1, the same defendant stole sensitive, nonpublic, and deliberative e-mails belonging to senior decision-makers responsible for Westinghouse’s business relationship with SOE-1.
As for the solar industry, in 2012 (roughly the same time the U.S. Commerce Department found that Chinese solar product manufacturers had “dumped” products into U.S. markets at prices below fair value) multiple co-conspirators “stole thousands of files including information about SolarWorld’s cash flow, manufacturing metrics, production line information, costs, and privileged attorney-client communications relating to ongoing trade litigation, among other things. Such information would have enabled a Chinese competitor to target SolarWorld’s business operations aggressively from a variety of angles.”
The indictment notes that the method of attack was the common approach of sending “spearphishing” email messages, designed to trick the recipient into giving the co-conspirators access to the victim’s computer. “Spearphishing messages were typically designed to resemble e-mails from trustworthy senders, like colleagues, and encouraged the recipients to open attached files or click on hyperlinks in the messages. However, the attached or linked files, once opened, installed ‘malware’—malicious code—that provided unauthorized access to the recipient’s computer…thereby allowing the co-conspirators to bypass normal authentication procedures in the future.”
To learn about basic cybersecurity practices for the power industry, see “Generation Cybersecurity: What You Should Know and Be Doing About It” in the February issue of POWER and a special report on NERC CIP Version 5 in the forthcoming June issue (online at powermag.com by June 2).
—Gail Reitenbach, PhD, Editor (@GailReit, @POWERmagazine)