The cybersecurity needs of the electric power industry are unique, due to the critical nature of the product and the wide range of technologies that must be considered—from complex, modern industrial control systems to aging infrastructure elements.
Smart grid technologies are introducing millions of new, intelligent components to the electric grid—such as those that enable two-way communications, dynamic optimization, and wired and wireless communications (Figure 1). These devices communicate in much more advanced ways than was possible in the past. Cybersecurity is increasingly important to our industry because the bidirectional flow of communication and control capabilities that will enable an array of new functionalities and applications also introduces new potential vulnerabilities.
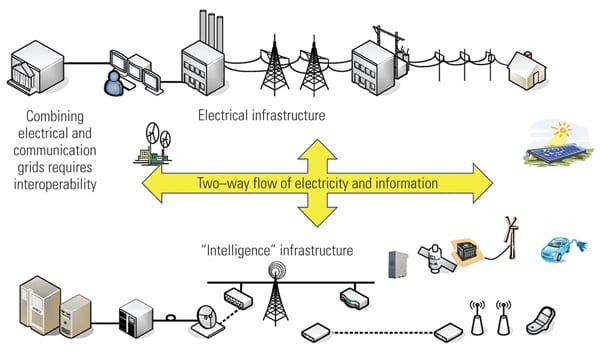 |
| 1. Smart grid = electric infrastructure + intelligence. Source: EPRI |
The interconnectedness of domains of the grid is also changing, as shown by the conceptual model of the smart grid illustrated in Figure 2. Another change is the interconnection of systems across organizations, for different purposes such as the export/import of electricity, providing situational awareness data, and receiving market data.
 |
| 2. Conceptual reference diagram for smart grid information networks. This conceptual model of the evolving smart grid includes potential communication paths and intra- and interdomain interactions. Source: National Institute of Standards and Technology |
For each utility, modernization of the electric grid will take many years, possibly decades to complete. Throughout this long transition period, legacy equipment will be operated in conjunction with new equipment. In the current grid environment, legacy SCADA systems may have limited or no cybersecurity controls in place. Whatever stage of modernization a utility’s transmission and distribution system is at, it must continually evaluate and plan to prevent and mitigate cybersecurity threats.
Cybersecurity Threats and Risks
Cybersecurity must address not only deliberate attacks launched by disgruntled employees, agents of industrial espionage, and terrorists, but also inadvertent compromises of the information infrastructure due to user errors, equipment failures, and natural disasters.
Potential risks to the grid include:
- Increasing the complexity of the grid could introduce vulnerabilities and increase its exposure to potential attackers and unintentional errors.
- Interconnected networks can introduce common vulnerabilities.
- Increasing vulnerabilities to communication disruptions and the introduction of malicious software/firmware or compromised hardware could result in denial of service or other malicious attacks.
- Increasing the number of interconnected digital devices increases the number of entry points and paths for potential adversaries to exploit.
- Interconnected systems can increase the amount of private information exposed and increase the risk when data is aggregated.
Figure 3 illustrates the paths that malicious and nonmalicious individuals may take to initiate a cybersecurity event. Control systems may be accessed directly or through corporate systems. Currently, the majority of cybersecurity events are nonmalicious. Regardless of the source of the cybersecurity event, the impact is likely to be the same: destabilizing the grid in unpredictable ways.
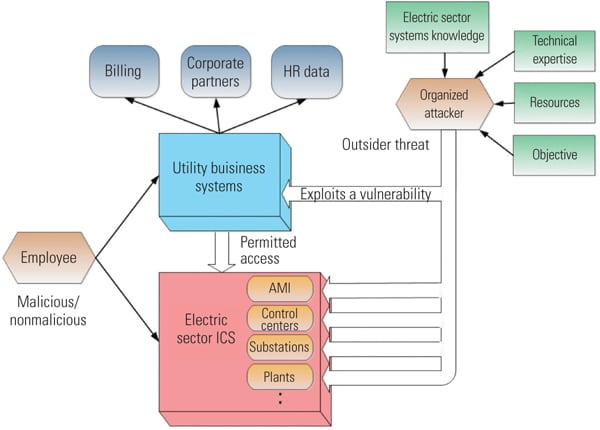 |
| 3. Anatomy of threat activity. Source: EPRI |
Developing a Cybersecurity Strategy
To adequately address potential threats and vulnerabilities, cybersecurity must be included in all phases of the grid system development life cycle—from design through implementation, maintenance, and disposition/sunset—and it must address prevention, detection, response, and recovery. Prevention is the first line of defense. But because cybersecurity prevention controls can be defeated, utilities have to be able to detect incidents, respond to mitigate damage, and recover systems and data in a timely manner.
A cybersecurity strategy must address not only deliberate attacks but also inadvertent compromises due to user errors, equipment failures, and natural disasters. It also must include both domain-specific and common requirements when developing a risk mitigation strategy.
Cybersecurity Risk Management Framework. The focus in the first phase of a cybersecurity strategy is to develop an overall cybersecurity risk management framework. Included in that framework are risk assessment and the selection and tailoring of cybersecurity requirements and measures/controls.
Typically, a cybersecurity risk management framework is a high-level framework that is common across the organization. This framework may be tailored at lower levels in an organization, such as for business and operational components.
Cybersecurity Risk Assessment Process. One component of a cybersecurity risk management strategy is the cybersecurity risk assessment. Risk is the potential for an unwanted outcome resulting from an incident, event, or occurrence, as determined by its likelihood and the associated impacts. Cybersecurity risk is just one component of organizational risk, which can include many types of risk (for example, investment, budgetary, program management, legal liability, safety, and inventory risk, as well as the risk from information systems). Because the smart grid includes systems from the information technology, telecommunications, and electric sectors, the risk assessment process is applied to all three sectors as they interact.
A cybersecurity risk assessment includes identifying assets, vulnerabilities, and threats and then specifying impacts. The output is the basis for the selection of security requirements and subsequent risk-mitigation strategies (security measures/controls). As with any assessment, a realistic analysis of the impact of inadvertent errors, acts of nature, and malicious threats is critical.
Specification of Cybersecurity Requirements. Security requirements may be used by strategists, designers, implementers, and operators of the electric sector such as utilities, equipment manufacturers, and regulators in the security lifecycle of an electric sector system.
Power system operations pose many security challenges that are not found in most other industries. In particular, strict performance and reliability requirements are needed by power system operations. Additional criteria must be used in determining the cybersecurity requirements before selecting and implementing cybersecurity measures/solutions. These additional criteria must take into account the characteristics of the interface, including the constraints and issues posed by device and network technologies, the existence of legacy components/devices, varying organizational structures, regulatory and legal policies, and cost criteria.
In addition, each utility’s implementation of cybersecurity requirements should evolve as a result of changes in technology and systems, as well as changes in techniques used by adversaries.
Selection of Cybersecurity Controls/Countermeasures. Once security requirements have been specified, a utility selects its cybersecurity controls/countermeasures. The security controls should be selected and implemented based on an acceptable level of residual risk.
For the risk assessment during the operations and maintenance phase, the major difference is to make decisions about residual risk and whether the risk should be accepted, avoided, mitigated, shared, or transferred. In addition, the definition of the security controls is at a more granular level of specificity than the security requirements.
And, because there will be some security breaches, attention should be given to response and recovery efforts.
Guidelines for Smart Grid Cybersecurity
To address the cybersecurity requirements for the smart grid, the Smart Grid Interoperability Panel Cybersecurity Working Group (SGIP CSWG), led by the National Institute of Standards and Technology (NIST), developed the NIST Interagency Report (NISTIR) 7628, “Guidelines for Smart Grid Cyber Security,” September 2010. (A pdf of the report can be downloaded from http://www.nist.gov/smartgrid/ index.cfm.)
NISTIR 7628 is for individuals and utilities that will be addressing cybersecurity for all smart grid systems in all operational domains—generation, transmission, and distribution. NISTIR 7628 includes an approach for identifying cybersecurity threats and risks and selecting and tailoring cybersecurity requirements. Such an approach recognizes that the electric grid is changing from a relatively closed system to a complex, highly interconnected environment. Each utility’s implementation of cybersecurity requirements should evolve as a result of changes in technology and systems, new threats, and changes in techniques used by adversaries. Approaches to securing cyber technologies must be designed and implemented early in the transition to the smart grid. That is, cybersecurity should be “built-in” to each smart grid system.
The first volume of NISTIR 7628 describes a cybersecurity strategy, including a risk assessment process, used to identify high-level security requirements. The volume also presents a high-level architecture followed by a logical reference model used to identify and define categories of logical interfaces within and across seven domains. High-level security requirements for each of the 22 logical interface categories are then described. The first volume concludes with a discussion of technical cryptographic and key management issues across the scope of smart grid systems and devices.
The second volume is focused on privacy issues within personal dwellings. This volume provides awareness and discussion of such topics as evolving smart grid technologies and associated new types of information related to individuals, groups of individuals, and their behavior within their premises. The second volume provides recommendations, based on widely accepted privacy principles, for entities that participate within the smart grid.
The third volume is a compilation of supporting analyses and references used to develop the high-level security requirements. These include classes of vulnerabilities defined by the working group and a discussion of the bottom-up security analysis that it conducted while developing the guidelines.
Research Continues
A number of research efforts related to cybersecurity issues are taking place throughout the industry. At the Electric Power Research Institute, research focuses on collaborative approaches to addressing emerging threats to an interconnected electric system. The initiative is also assessing technologies for data privacy. For example, EPRI is conducting a project to develop standard security objects for automated metering infrastructure (AMI) systems. This would allow third-party vendors to develop security applications to use and display the alerts generated by the meters to provide better situational awareness to AMI operators. EPRI is also developing a “how-to” for NISTIR 7628, to provide practical guidance for utilities that are addressing cybersecurity issues related to grid modernization. â–
— Annabelle Lee (alee@epri.com) is EPRI’s technical executive for cybersecurity.