The North American Electric Reliability Corporation (NERC) on Thursday issued a recommendation to the electric power industry providing sensitive information about the so-called “AURORA vulnerability”—gaps in critical infrastructure protection concerning large motors and generators connected to the bulk power system.
The “technical library,” available at the “For Official Use Only” (FOUO) classification level by NERC’s federal partners, are located on protected sites on the NERC Regional portals for industry use. NERC requires potentially affected entities, including generator and transmission owners and operators, to report on efforts and progress by Dec. 13 and to provide updates every six months until mitigation is complete.
According to NERC, the recommendation developed by the AURORA Technical Team highlights detailed engineering data and new understandings of the issue. The mitigation elements that have been recommended fall into two broad categories: Protection and Control Engineering Practices and Electronic and Physical Security Mitigation Measures, the quasi-public agency said.
“While there is no single answer to the AURORA vulnerability, these recommendations offer asset owners options to develop and test in their own environments,” said Mark Weatherford, vice president and chief security officer at NERC. “NERC continues to work with government and industry experts to provide information to the industry as it becomes available.”
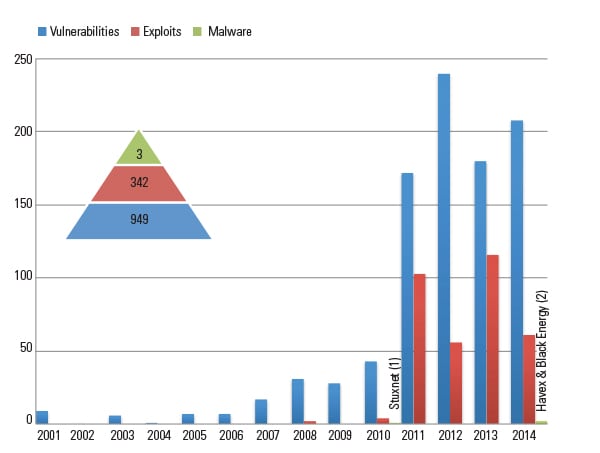
The agency initially issued a notification to the industry on the AURORA vulnerability on June 21, 2007, which was based on information available at the time. Since that time, NERC has worked with its federal partners to establish a technical library that entities can use to understand the complexities of AURORA at an engineering level.
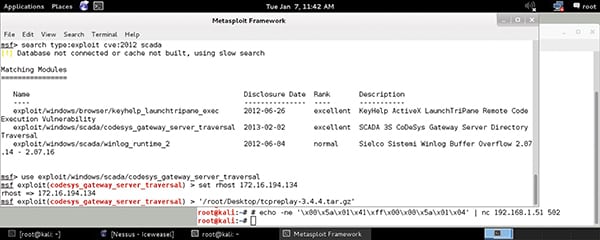
NERC confirmed to POWERnews that the vulnerability was not related to the Stuxnet worm—malware that seeks to attack supervisory control and data acquisition (SCADA) systems. However, NERC’s manager of critical infrastructure protection (CIP), Tim Roxey, told NetworkWorld that the newly released guidelines concern every aspect of power plant operations in terms of networks and physical security. He said they include everything from changes in dial-up modems to operating systems used for controls, though the guidelines do not apply to business systems.
Sources: NERC, POWERnews, NetworkWorld