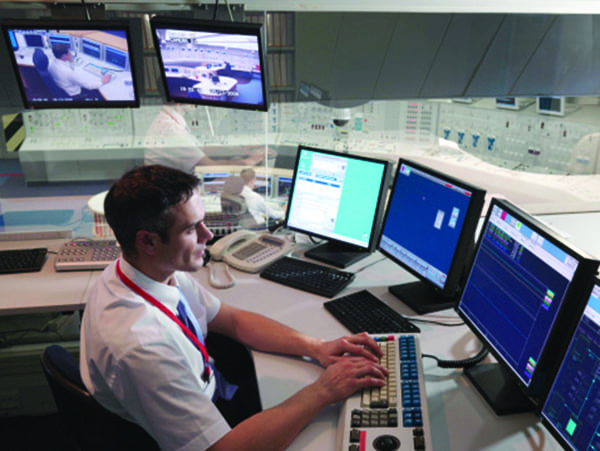
The Federal Energy Regulatory Commission (FERC) has proposed a revision of the Critical Infrastructure Protection (CIP) Reliability Standards to enhance awareness of existing or developing cybersecurity threats to the nation’s energy infrastructure.
FERC issued a Notice of Proposed Rulemaking (NOPR) on December 21 that directs the North American Electric Reliability Corp. (NERC) to broaden CIP-008-5 (Cyber Security—Incident Reporting and Response Planning) and include mandatory reporting of cybersecurity incidents that compromise, or attempt to compromise, a responsible entity’s Electronic Security Perimeter (ESP) or associated Electronic Access Control or Monitoring Systems (EACMS).
Under the current reliability standard, incidents must be reported only if they have compromised or disrupted one or more reliability tasks, FERC said.The proposal requires reporting of certain incidents even before they have caused such harm or if they did not themselves cause any harm.
“FERC is concerned [ the threshold under current standards] may understate the true scope of cyber-related threats facing the grid. In particular, the lack of any reported incidents in 2015 and 2016 suggests a gap in the current mandatory reporting requirement. The 2017 State of Reliability report by [NERC] which is responsible for enforcing FERC-approved mandatory reliability standards, echoed this concern,” the agency added.
The proposal would also require NERC to modify the CIP reliability standards to specify the required information in cybersecurity incident reports, mainly to improve the quality of reporting and allow for ease of comparison as well as establish a deadline for filing a report once a compromise or disruption, even if attempted, is identified by a responsible entity.
The rule proposes that these incident reports should then be sent to the Electricity Information Sharing and Analysis Center (E-ISAC). Entities should also send reports to the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT). NERC would also be required to file an annual, public and anonymized summary of the reports with FERC.
The measure stems from a January 2017 petition filed by the Foundation for Resilient Societies, a nonprofit group dedicated to the protection of critical infrastructure from disaster. The group’s petition urged FERC to require an enhanced reliability standard for malware detection, reporting, mitigation, and removal from the bulk power system, noting that power plants and the grid are increasingly at risk from malware. Current mandatory and voluntary reporting methods “underreport the actual annual rate of occurrence of cybersecurity incidents in the U.S. electric grid,” the group said.
Specifically, the group claimed that cyberattacks on systems outside the ESP can take down systems within it and that electronic access points that control access to systems within the ESP may be breached. It also noted that there is currently no required reporting of malware infections both inside and outside of the ESP.
FERC noted in its NOPR that a number of commenters—among them NERC, the International Transmission Co., and several major power industry groups, including the Edison Electric Institute, the Electric Power Supply Association, and the American Public Power Association—urged the agency not to act on the Resilient Societies’ petition. The commenters claimed that the issues raised by the group are adequately addressed in the CIP Reliability standards or modifications to current standards under development. NERC specifically identified seven currently effective CIP requirements that it said addressed the risks associated with malware—as well as standards being developed in response to two 2016 FERC orders (Order No. 822 and 829).
FERC ultimately declined to act on the Resilient Societies’ call for new standards to address malware detection and mitigation. However, it determined that the current reporting threshold for cybersecurity incidents as set forth in the current definition of “Reportable Cyber Security Incident” may “not reflect the true scope of cyber-related threats facing the bulk power system, consistent with NERC’s view.”
Comments on the NOPR are due 60 days after publication in the Federal Register.
—Sonal Patel is a POWER associate editor (@sonalcpatel, @POWERmagazine)