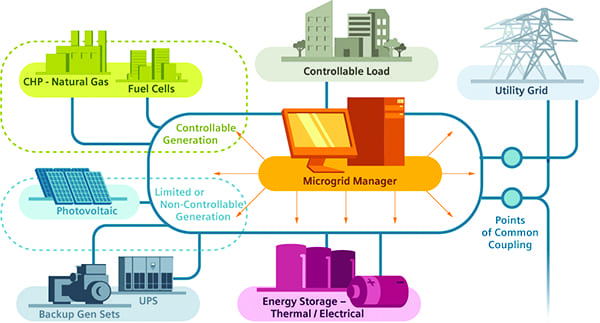
Anyone who follows either the energy industry or the military knows that all branches of the U.S. military have aggressive goals for renewable energy and for improving energy security and independence. Microgrids are a key part of that plan.
When I wrote about military microgrids in “The Military Gets Smart Grid” back in January 2012, I noted that the U.S. military had the need, money, ability, track record, and systems thinking to deploy smart grid technologies, especially microgrids. At that time, there was talk about collaboration between the Department of Defense (DOD) and the Department of Energy (DOE) that would, among other things, use DOD facilities as test beds for new smart and microgrid technologies, enabling those cutting-edge devices to reach the commercial market faster
For multiple reasons, things haven’t quite worked out that way, according to speakers at the 4th Military & Commercial Microgrids Summit in Washington, D.C., held June 17 to 19.
Testing, Testing, 1, 2, . . .
Small-scale “test bed” projects are under way, explained Dr. James J. Galvin, program manager for the DOD’s ESTCP (Environmental Security Technology Certification Program) Energy & Water Program. Most are research and development (R&D) projects at fixed bases in the U.S. They include a dining facility microgrid project at Fort Bliss in Texas, which is being used primarily to reduce peak demand charges from the local utility.
Within the DOD, two-thirds of the test bed strategies, Galvin said, are focused on building technologies, and most of the microgrid, storage, and demand response efforts are concentrated in southern California and Texas.
Not all test bed projects pan out. A wood chip gasifier tested at Fort Carson in Colorado Springs, for example, proved too expensive to continue operating. Though it provided renewable biomass power, the 12¢ to 14¢/kWh was no match for 5¢/kWh from the local utility.
And using military installations to test emerging technologies poses additional timing and coordination challenges. A California site hoping to test zinc bromide flow batteries is experiencing delays “to get the technology refined,” Galvin said. “We’re being patient with this one,” he added.
The military is a different type of customer in many ways. Even the integration of electric vehicles, whose batteries can be used to store energy from on-site renewables, poses a scheduling challenge. Obviously, combat vehicles can’t be relied upon for storing microgrid energy, but the scheduling constraints have proven problematic even for administrative vehicles.
What’s the Security Policy?
Then there are security concerns. The military doesn’t want outsiders (including utilities) anywhere inside its systems. One solution currently being used is a “middleware panel” that sits between buildings and business-side servers to allow interface with multiple legacy systems.
Technology needs to be open and adaptable, not proprietary (not just for military purposes), advised William C. Anderson, strategic development executive for the government segment at Eaton Corp.
Teasing a similar thread in another session, Jeff Johnson, Naval District Washington command information officer, strongly encouraged diversity of devices (because they broaden the threat vector) but the ability to control that range of devices with one system.
Multiple speakers agreed that security needs to be “baked in” to microgrid components. Dr. Richard B. Andres, professor of national security strategy at the National War College, observed that the tendency in the past has been to “skimp” on security. That attitude is dangerous today, when—as the national security advisor to the Senate has argued—the cyber threat is a bigger threat to the nation than the economy or anything else, Andres continued.
During a Q and A session, panelists were asked for their top three questions for vendors that would help determine how cybersecure their microgrid systems are. Responses (most of which also would apply to nonmilitary systems) included:
- What’s the patching system?
- Does the contract include a right to audit?
- Do devices communicate with one of the approved DOD protocols?
- Have the devices been independently tested and certified?
- Does it use open architecture?
- What’s your continuous monitoring strategy?
- What standards are you compliant with?
- What’s your defense-in-depth approach?
Harry Regan, director of Securicon LLC, reminded attendees not to forget physical security—everything from cables and servers on racks to access doors. The “area that is usually the first point of attack is people,” he said. They “open doors for you,” sometimes quite literally, say, if you are carrying a box. A “young girl with a hard hat and a clipboard has an 80% chance of getting through” a supposedly access-protected door, he claimed.
Dr. Jason E. Stamp, distinguished member of the technical staff at Sandia National Laboratories, provided an update on the SPIDERS (Smart Power Infrastructure Demonstration for Energy Reliability and Security) microgrid project—which involves the DOD, DOE, and Department of Homeland Security. SPIDERS focuses on “design-basis threats.” The project has three main locations: Hickham Air Force Base and Camp Smith in Hawaii and Fort Carson in Colorado. The Hickham project is furthest along. Systems there operate “as intended” and site personnel can manage the microgrid, Stamp said.
Keep It Simple
Referring to an early “snafu” that was training-related, Stamp observed that microgrids, especially on military installations where personnel cannot necessarily be pulled from mission-critical tasks to operate a microgrid, have to be simple to control, operate, and maintain.
There are “no technical reasons” that microgrids can’t work, Stamp said; it’s the integration piece that poses challenges—a refrain that was heard throughout the event.
The types of projects that seem to work best are those that are also most familiar outside the military fence.
The main smart grid/microgrid goal for the military is “affordability down the road 20 to 30 years,” explained Donna Carson-Jelley, utilities and energy systems smart energy program director for the U.S. Navy. The Navy is looking at “already done” technology, not R&D projects, that have “customizable” smart grid technologies and controls.
The Financing Conundrum
Jody Davenport, PE, program manager for the U.S. Navy’s Naval District Washington, noted that there have already been some valuable benefits of smart grid technologies. The Navy got early return on investment from advanced metering infrastructure just by having data to make decisions.
But, as demonstrated by the abandoned Fort Carson test bed project described earlier, not all advanced technologies can be economically justified, especially given military budgets and their rules.
In a financing panel, Jeff Weiss of Distributed Sun LLC, said that microgrids are “largely illegal” on military installations because facilities are not allowed to spend more than they would on grid power. Jamie Link, in business development with EDF Renewable Energy, added that those cost constraints make a holistic approach necessary, especially with military microgrids, and make the provision of ancillary services to the grid important to the business case.
William C. Anderson, strategic development executive for the government segment at Eaton Corp., argued that there hasn’t been sufficient R&D on advanced grid technology, but the “government is broke,” he said, so a different approach is needed. He advocated engaging private partners from state, local, community, utility, and financial sectors to develop primarily grid-tied distributed generation and microgrids that could help support the traditional grid.
Proven Value
Captain Clifford Maurer (Ret.) of the Civil Engineer Corps, U.S. Navy, said he was “buoyed” by what he’s heard the past couple of years at microgrid conferences. He spoke on a panel about what the military can learn from one of the most cutting-edge and comprehensive microgrids, at the University of California, San Diego.
Maurer observed that when the utility grid experienced a blackout on Oahu, “not for 1 second did we lose any military capabilities,” thanks to onsite generation at Camp Smith. However, the current manual disconnection/islanding process could be improved, he noted.
The ability to generate power with onsite fuel (wind and solar), store that energy (with various storage technologies), control loads to optimize power use (via smart meters, sensors, and controls), and disconnect from the grid all offer powerful incentives for the development of military microgrids. The cost of individual components with a proven track record is becoming less of a barrier. Whether and when the necessary policy components see realignment—from cost-of-power restrictions to impediments introduced by local distribution utilities—is anyone’s guess.
For more reporting on this event, see:
The State of the Microgrid Market: Promise and Present Realities
Interest Growing in Commercial and Community Microgrids
Islands Are the Low-Hanging Fruit for Microgrids
—Gail Reitenbach, PhD, Editor (@GailReit, @POWERmagazine).