Over the last few years, it has become increasingly clear that a massive cyber-attack on the North American electric grid represents a serious threat to U.S. national security. Over time, a string of senior U.S. officials have labeled this threat one of the most serious faced by the nation and warned that not enough is being done to deal with it.
A “Hidden” Threat
The basic problem is that the type of threat that is emerging is new; there is little existing organizational or administrative structure in government or private industry to deal with it. It is compounded by the secrecy surrounding cyber weapons strategies, which, unlike conventional and nuclear weapons, depend almost entirely on secrecy. Nations develop and employ them but virtually never talk about them; companies find them on their infrastructure but are reluctant to admit having been attacked.
The notion that cyber weapons could be used to take down power grids is not new, but it first received widespread public attention in June of 2010, when reports began to surface that a virus called Stuxnet had attacked the supervisory control and data acquisition (SCADA) system controlling Iranian nuclear centrifuges and eventually destroyed their hardware. Two particular aspects of the attack drew the attention of the electricity industry. The first was that, as the virus was destroying hardware, it remained undetected on the system for years. The second was that the Siemens SCADA infrastructure that it took over was similar to the systems that control much of the world’s electrical infrastructure. In the wake of Stuxnet, the electricity industry began to look inward and discovered that Stuxnet and other malware were resident on a large proportion of their own industrial control systems.
Potentially Catastrophic Consequences
From the perspective of national security, the discovery that North American electricity infrastructure is infested with malware designed to destroy hardware was momentous. The U.S. grid is built around a small number of ultra-high-voltage transformers and other difficult-to-replace physical choke points. It would be extremely tough, but far from impossible, to turn off sensors on equipment or use other methods that would lead to the simultaneous destruction of large portions of the grid’s generation and transmission capability. In some scenarios, such an attack would leave most of the country without power for months or years.
The effects of this type of outage would be catastrophic. In the first few minutes of a national outage, virtually all commerce would cease as electronic systems went down. Gasoline pumps would stop. Telephones, including those used by government and emergency responders, would quickly cease functioning. Cities that use electricity to pump water would lose water pressure, and sewage systems would back up into fresh water. Fuel pipelines would cease to function. Most households have three days of food available and no stored potable water. Hospitals would continue to function for a few days. National Guard and law enforcement agencies have stated on the record that they believe their employees would stop coming to work after less than a week. Disease and starvation would set in within days.
The amount of damage a scenario like this would cause to property and life would depend on the size and duration of the outage. So long as the blackout was small enough to allow affected persons to exit the region and repair teams and emergency responders from unaffected regions to enter, the loss of life could be minimized. However, recent experience with the power outage following Hurricane Sandy in 2012 suggests that the affected area would not have to be particularly large to delay repair and emergency response teams. A worst case scenario months-long-continent-wide outage would claim millions of lives. Even smaller and shorter outages, however, could be devastating.
Taking down the grid would most likely require the resources of a major power. Such states are usually deterrable. Unfortunately, cyber weapons technology is evolving faster than cyber defenses, and what is only possible for great powers today will be possible for smaller states tomorrow. The U.S. has gone to war roughly six times since the end of the Cold War, always against enemies that lacked the ability to retaliate. The vulnerability of the North American electric grid to cyber-attacks represents a cheap way to project power and an irresistible temptation to a wide swath of America’s potential opponents.
It’s Not Too Late
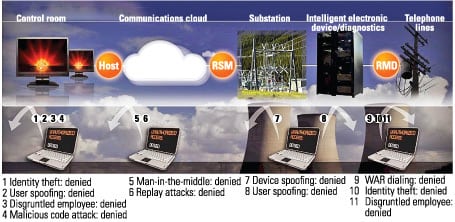
All is not lost. Taking down the grid would be difficult, and much can be done to make it harder yet. Industrial control systems and SCADA infrastructure can be better protected. Industry can share more information on cyber-attacks and empower the Federal Energy Regulatory Commission and North American Electric Reliability Corp. to develop stricter mandatory standards. Local power generation can increase its islanding and black-start capability.
At the moment, most companies are at least peripherally aware of the problem. However, industry leaders appear to be waiting for a massive event to spur them to action. This strategy is risky. If such an event were to occur, it would, at the least, raise questions about why industry did not protect the lives of its customers and would most likely lead Congress to rethink private ownership of electrical infrastructure. This would be in no one’s interests. The time to act is now. ■
— Richard B. Andres is professor of national security strategy at the U.S. National War College and senior fellow at the Institute for National Strategic Studies.