The number of cyber attacks on operational technology (OT) is rising rapidly. What was once a concern primarily reserved for information technology (IT) professionals has moved into OT spaces. The proliferation of connected devices in OT environments has opened the door to critical infrastructure for bad actors looking for payouts, to cause harm or gain recognition. Despite the growing risk of attack, nearly half of industrial control system (ICS) organizations lack internal teams dedicated to managing their OT.
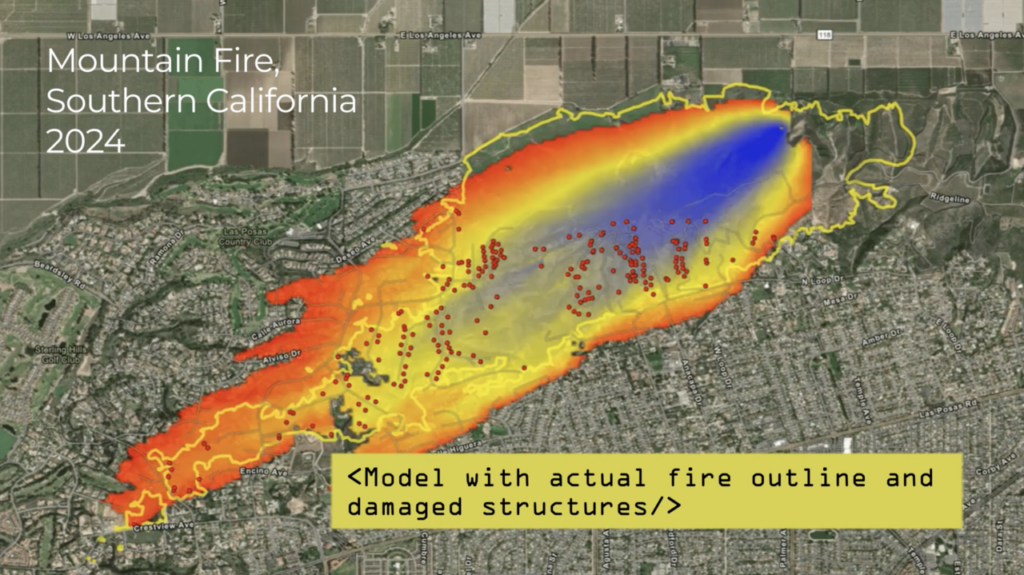
This confluence of factors can put everyone at risk. When attackers do gain access to OT systems, the results can be devastating. Unlike attacks on IT environments, those in OT can often have physical consequences to lives and livelihoods. While a breach of a subscription-based website’s customer database might result in stolen credit card numbers or hacked email accounts, attacks on water treatment plants, fuel pipelines, or ports can mean tainted water, energy shortages, or sunken ships.
To combat this growing problem, large-scale factories, government contractors, critical infrastructure sites and other at-risk facilities are taking steps to improve their cyber hygiene—but those steps are rarely big enough. These businesses are investing in zero trust for OT networks (ZT4OTTM) and other modern IT cyber technology to help protect OT infrastructure and mitigate the risk of a cyber attack. However, cybersecurity measures that protect IT environments from breaches are not generally applicable in OT environments.
The differences between OT and IT cybersecurity programs can often go unrecognized but understanding them can make all the difference when an attacker is looking for an opening. Without specialized equipment, tailored processes and highly experienced teams leading the charge, cybersecurity protocols are likely to be left wanting.
Components of a sound OT cyber program

Many organizations are unsure of where to begin when building out an OT cybersecurity program. The answer? Start at the beginning. OT environments are best protected when OT systems and networks are identified, so that any update, upgrade or renovation must have cybersecurity protocols built in from day one. All is not lost for organizations that need to update security protocols within their existing facilities; they just need to do a little more legwork. That means hiring an experienced team specialized in OT security who can:
- Create a comprehensive asset inventory. Shockingly few organizations have visibility into the composition of their OT network—and you can’t protect what you can’t see. Auditing the network to identify every device (connected or not) is the best way to build a cybersecurity plan that accounts for every possible point of attack.
- Map those assets. Knowing what’s there is just the first step. Facility operators should also understand how each asset interacts with the rest of the network. Even assets that are updated via supplier USB drives or vendor maintenance should be noted as those points of connection can still pose risks.
- Evaluate vendors and suppliers. Your OT environment could be the most secure and tightly controlled in the world, but one supplier that’s unprotected can open you up to potential threats.
- Implement monitoring processes. Once a company has visibility into these areas, it can track changes and monitor for abnormalities. Identifying OT attacks as the work of bad actors can be difficult as they often appear as malfunctions. With this in mind, tracking all activity is crucial to identifying breaches and addressing them before hackers use their access to wreak havoc.
- Develop a response plan. Despite the risks, many operators believe that a breach won’t happen to them—and they don’t know how best to respond when it eventually does. All OT environments should have pre-developed response plans that account for attacks that harm employees, are executed for ransom, or result in downtime.
The power of a good partner

As already noted, many organizations lack teams that are dedicated to OT cybersecurity—and hiring the right one isn’t easy. Because of the sector’s relative immaturity, experts in OT cybersecurity are few and far between. That’s where a dedicated managed security services provider (MSSP), like ABS Group, can help. With decades of experience in operational risk in greenfield and brownfield projects, ABS Group’s expertise can help operators across sectors rest easy knowing they’re protected.
SWOT24™, OT Cybersecurity by ABS Group, can provide an industrial cybersecurity program for organizations that do not have adequate controls in place. SWOT24 monitors all activity 24/7/365 from ABS Group’s centralized industrial security operations center (ISOC) with no interference in clients’ operations. Once the SWOT24 team installs passive monitoring equipment in a company’s operational network, the client will receive company- or fleet-wide monitoring coverage for OT and ICS networks and devices.
SWOT24 customizes its OT cybersecurity solutions based on a client’s business objectives and operating environments so vulnerabilities can be addressed and any immediate threats can be escalated to leadership promptly. SWOT24 services include:
- Managed Services, to help with the implementation and execution of a company’s OT cyber program, aided by the 24/7/365 support of the ISOC.
- Supply Chain Cyber Risk Management, to help companies assess their up- and downstream risk.
- Cybersecurity for New Construction, to help operators design OT environments that are secure by design.
- Zero Trust for OT Networks (ZT4OTTM), to spearhead the development of zero-trust architecture for OT environments.
- Specialized Consulting, to meet other client needs with tailored support.
SWOT24 offers a comprehensive portfolio of OT cybersecurity consulting and risk management services to help organizations identify and mitigate critical cyber threats in real-time. ABS Group’s experts focus on helping to deter and prevent the bad guys so companies can focus on what really matters: their operations.
To learn more about SWOT24 and ABS Group’s services, visit www.abs-group.com/SWOT24