We have reached a turning point. Cybersecurity is no longer the domain of the experts, it’s a distributed responsibility across the whole organization. It’s critical for each company in every sector, but electric utilities have some unique attributes that make cyber resiliency the highest priority and network managers of the utmost importance.
Utility Network Managers & Cybersecurity
As network managers, we sit at a critical intersection: our infrastructure carries the data that keeps the grid stable, and our decisions directly influence the organization’s cyber resiliency. The security team may set policy and drive strategy, but we own the networks that must withstand real world threats.
We must, and I cannot stress this enough, be proactive. It’s how we prevent outages, maintain compliance and ensure that our systems remain reliable in the face of increasingly sophisticated adversaries. The following principles outline how network teams can strengthen their role in cybersecurity while aligning with NERC CIP expectations.
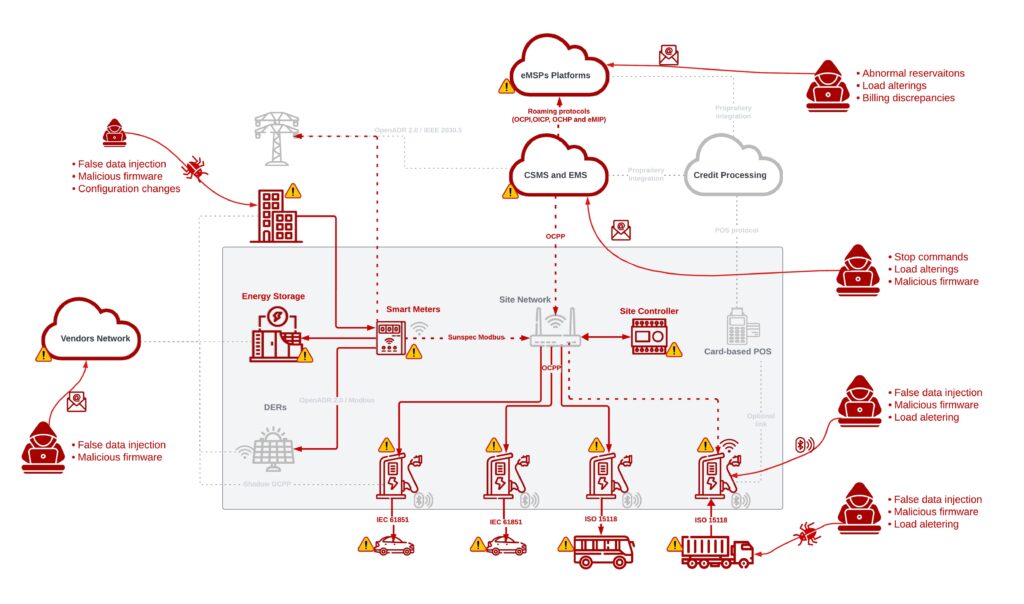
It All Starts with Visibility of Network Components
You can’t protect what you can’t see. Network visibility is the foundation of every security control—monitoring, detection, segmentation and incident response all depend on it.
This means understanding every switch, router, firewall, wireless bridge, serial gateway and virtual interface. It means knowing which assets are routable, which are dual homed, and which are quietly bridging networks you didn’t intend to connect.
Visibility tools help, but they don’t replace engineering awareness. Walkdowns, diagrams and periodic reviews are essential. Creating network diagrams is a requirement under NERC CIP-002-3 but beyond that they are a critical resource—and must be kept up to date.
Mature commercial scanning solutions exist to help—deploying even one provides a clearer picture of your exposure.
An Accurate Inventory Is a Must
A complete, accurate inventory is a compliance requirement, but more importantly, it’s a security necessity. Whether it’s a spreadsheet or a formal CMDB, at a minimum basic device information should be maintained:
- Hardware model and serial.
- Operating system and firmware version.
- Installed modules and cards.
- Network interfaces and IP assignments.
- Physical location.
- Criticality classification.
- Support contracts and end-of-life dates.
Capture it at installation. Keep it current through every change.
Patching Every Day Helps Keep the Bad Actor Away
Patching is one of the most effective defenses against cyber threats, yet it’s also one of the most operationally challenging in the corporate network and even more so across industrial control systems (ICS). Downtime windows are limited, vendor support varies and testing is essential.
Start with routine scanning which, in coordination with operations, helps identify exposures early. Even when scanning is restricted in certain environments, passive scanning tools and vendor advisories can fill the gap.
Not all vulnerabilities are equal. CVSS scoring helps to prioritize based on severity, exploitability and impact. A CVSS 10 affecting a perimeter firewall demands immediate attention; a CVSS 4 on an isolated serial-to-Ethernet converter may be acceptable until the next maintenance window. The key is documenting the rationale and ensuring decisions align with risk tolerance and CIP requirements.
Standard Configuration-A Step Toward Maturity
Standardized configurations reduce risk by eliminating guesswork. Templates for switches, firewalls and routers ensure consistent:
- Logging.
- Time synchronization.
- Access control lists.
- SNMP settings.
- Encryption standards.
- Interface naming conventions.
When every device follows the same baseline, deviations become easier to spot — and attackers have fewer opportunities to exploit misconfigurations.
Access Control
Access control is more than passwords and accounts. It includes:
- Role-based access.
- Multi-factor authentication where feasible.
- Jump hosts and secure remote access pathways.
- Least-privilege principles.
- Timely removal of unused accounts.
Network teams must enforce these controls and ensure that privileged access is monitored and auditable. This is truly a case whereby helping others, the network engineers help themselves.
Cybersecurity/IT Integration with Network Management
Cybersecurity isn’t something that happens “over there.” The cyber team’s strategies, tools and expectations directly affect network operations. Whether it’s deploying sensors, enabling logging or participating in tabletop exercises, network teams play a central role in executing the cyber program. Active support and participation from the network team is needed and expected.
Design
Design is listed last, but in practice it’s the beginning of everything. Strong cybersecurity starts with architecture. You are the networking experts but coordinating early with the cyber team prevents rework and ensures that new systems meet both operational and security requirements.
If not done already, segment your network. Segmentation is one of the most powerful tools we have. Properly designed zones and conduits limit lateral movement and contain incidents before they spread.
Consider implementing threat modeling exercises. Ask your cyber team to walk you through their penetration testing results. The gaps they find are yours to close.
As network managers in a NERC CIP environment, we’re not just maintaining infrastructure; we’re safeguarding the reliability of the electric grid. Cybersecurity is woven into every cable, every configuration and every change request.
The security team may lead the strategy, but we are the ones who make it real. When we embrace that responsibility, collaborate proactively and design with security in mind, we strengthen not only our networks but the entire organization.
—Alan Hirth is Group Manager, Grid Automation Practice, for Actalent Services.