Cyber Threats Proving Their Power over Power Plant Operational Technology
The threats to power industry operations—and the reliable supply of power that we all depend upon for daily life—are no longer theoretical. A roughly 250% spike in reported industrial control system incidents over the past four years demonstrates that regulations alone will not protect power infrastructure. Everyone who works in this industry needs to develop higher awareness and skills.
As a longtime cybersecurity professional, it has been interesting to observe the progression of conversations about cybersecurity and the technology advances made by industry colleagues. Perhaps most dramatically, for the first time, the issue of cybersecurity recently has become a mainstream topic of conversation worldwide.
While the practice of cybersecurity—the actual business of protecting personal, business, or government networks and computers—has been around for more than 30 years, events over the previous two years have brought a sharper focus to growing challenges and concerns. Whereas past conversations focused merely on the need to have an appropriate level of cybersecurity to protect Internet-connected systems, today businesses are also asking, Is there a model of cybersecurity that can protect an organization against targeted attacks?
The answer is yes, but the execution of protective measures can be complicated, and the details are beyond the scope of this article. What’s important to note is that business leaders are beginning to understand the connections between the increasingly common attacks on consumer-facing businesses and how those attacks are related to potentially more disruptive attacks on industrial systems and critical infrastructure. This article reviews recent changes in and frequency of cyber attacks as well as steps being taken—and still needed—to protect power industry operational technology.
Heightened Public Awareness
There is no better example of how cybersecurity has taken its place at the forefront of people’s minds than the recent attack on Sony Pictures, in which sensitive emails, as well as employees’ Social Security numbers and private medical information, were revealed for anyone in the world with Internet access to see. The attackers, who the U.S. government has since identified as having connections to North Korea, even succeeded in stealing Sony Pictures films, such as Fury and the remake of Annie, disrupting the business model of bringing movies, in various forms, to market.
While corporate giants such as JPMorgan Chase, Target, and Home Depot also fell victim to devastating cyber attacks over a 16-month period, it was the attack on Sony Pictures that one can argue is most responsible for the heightened public awareness of and attention on cybersecurity. “If we don’t put in place the kind of architecture that can prevent these attacks from taking place, this is not going to just be affecting movies, this is going to affect our economy in ways that are extraordinarily significant,” said President Barack Obama.
It is estimated that over 56 million credit and debit cards as well as 53 million personal email addresses were compromised in the April 2014 cyber attack on Home Depot; as a result, community banks across America are on the hook for around $90 million in costs associated with credit card reissuing fees, according to a recent report in SC Magazine. Likewise, the JPMorgan Chase hack lasted for over three months and so far has negatively affected more than 75 million households worldwide.
But these corporations are not alone. Although damages are difficult to precisely calculate, some studies suggest that cyber crime accounted for over $995 billion in losses worldwide in 2013, and the numbers for 2014 are certain to be similar, if not more devastating to the bottom line.
It’s important to realize that the primary motivations for the cyber crimes committed against Home Depot, Target, JP Morgan Chase, and the thousands of other corporations breached, while highly destructive in their own ways, were executed with economic gain as a primary objective. The unintended consequences of such attacks, however, are that the public’s awareness of cybersecurity, while much heightened, is now overly limited to the threats against their wallets and, to a lesser extent, vulnerabilities of their Internet communications.
While the attacks against Sony Pictures did include motivations that went beyond financial gain, the attackers were most set on destroying value. This took the form of undercutting business models through damaging releases of products, information, and the destruction of data.
It is important to remain conscious of, and take the necessary precautions against, the type of hacks that can affect the ordinary consumer’s wallet. But there is another type of cybersecurity threat—one that targets an organization’s or a nation’s infrastructure—that cybersecurity and national defense professionals agree has the most potential to introduce severe harm.
Realizing the Threats to Power Infrastructure
In December 2014, Cylance, a global security services and products company, released the findings of a two-year investigation into a cyber attack campaign. Named Operation Cleaver, the report cited significant evidence that Iran has operated a sustained campaign to gain control of sensitive computer networks, including those of military institutions, defense facilities, general aviation facilities, oil and gas producers, and, of course, power utilities. The report says that the risk that Iran is “gearing up for the probability of an attack that could impact the physical world at a national or global level is rapidly increasing.”
The Cylance report came on the heels of an address given by the incoming Director of the National Security Agency and Commander of the U.S. Cyber Command, Navy Admiral Michael Rogers. Rogers told members of Congress that, “what we think we are seeing is reconnaissance by many of those actors in an attempt to ensure they understand our systems, so that they can then, if they choose, exploit the vulnerability within those control systems.” The admiral has since made remarks in which he suggested that China has the capabilities to sustain an attack on U.S. power grids.
Similar to an attack on a corporation, a successful hack into the networks within critical infrastructure also has the capability to victimize individuals severely. As you know, utilities maintain a tremendous amount of information about their customers, arguably more than retail and other services companies. In order to get power, for example, a person must provide a credit score, home address, personal banking, and other sensitive information.
But that’s where the similarities end. Unlike an attack on systems holding account information, should an attacker successfully infiltrate critical infrastructure, the primary motivations likely exceed economic ones, as the incentives of such attacks are much more likely to be the threat of disruption to operations—by hindering public safety and productivity—within the foundational systems that keep a nation in service. An attacker willing to intrude upon a nation’s infrastructure or attempt to cause economic damage by destroying value has decided to risk a proportional response. As an example, the Obama administration announced that it has imposed additional sanctions on North Korea in response to the attacks on Sony Pictures.
Threats Evolve with Greater Interconnection
The power industry, like the rest of the world, is increasingly becoming digitally connected (Figure 1). Historically, operational technology (OT), like industrial control systems (ICS), was standalone and did not have cyber interconnectivity. In recent years, new technologies, such as data-driven analytic applications and cross-platform communications, have been added to industrial systems to increase productivity and achieve greater levels of reliability. This has been done despite legacy systems not being originally designed to integrate with such technologies.
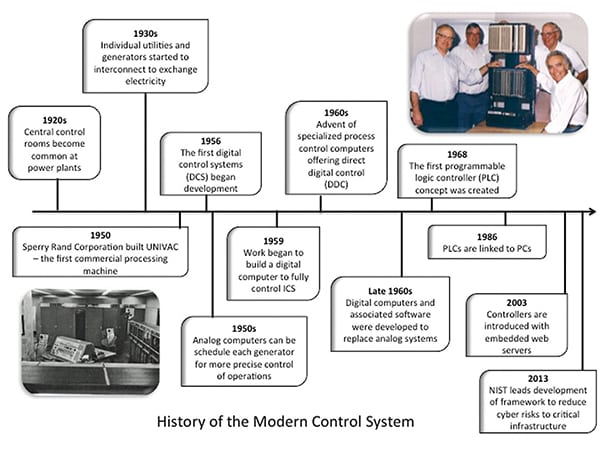 |
| 1. A brief history of the modern control system. Courtesy: NexDefense |
Modern automation and control systems now connect to business networks and external systems to allow operators and suppliers to remotely control, monitor, and maintain every aspect of operations, ultimately improving productivity, enhancing performance, and reducing costs. Communications technology is also used to tap into an extended global supply chain and more tightly couple manufacturing and infrastructure operations to the global marketplace. While these advancements improve efficiency, they also create new attack surfaces, introduce complexities, and expose vulnerabilities for attackers to exploit.
Prior to the adoption of connected digital systems, an adversary would need to be physically on site in order to compromise a control system or rely on people to walk their attacks into production systems. Introducing interconnected systems and remote access technology provides someone with malicious intent the ability to gain access to production networks from anywhere in the world.
Threatening Core Generation Operations
Attacks on critical infrastructure operators can disrupt operations and equipment that provide essential services to communities. “There are those industrial control systems that can shut down and forestall our ability to operate… basic infrastructure, whether it’s generating power across this nation, whether it’s moving water and fuel,” Adm. Rogers told Congress.
Digital advancements in OT allow the power industry to more efficiently generate, transmit, and deliver electricity. However, a destructive cyber attack on these systems would challenge the core ability to operate safely and reliably. Threats to these systems create a reduced sense of predictability and heightened concern for safety. A successful attack on industrial systems may not only affect the control system. An attacker can directly affect the process and maliciously operate controlled equipment, raising safety concerns. Loss of intellectual property, as in the Sony Pictures case, is a very different consequence than losing visibility or control of an industrial process.
Threats to critical infrastructure OT are no longer theoretical, and their existing vulnerability is an area that actors are actively exploiting. In October last year, the Department of Homeland Security’s (DHS) Industrial Control System Computer Emergency Response Team (ICS-CERT) alerted critical infrastructure asset owners and operators of a cyber campaign called BlackEnergy 2 and its use of ICS-capable malware modules targeting numerous ICS products that have been in the wild since at least 2011 (Figure 2). On Nov. 20, Adm. Rogers testified on Capitol Hill that multiple nation states have the ability to infiltrate control systems and cause catastrophic failures.
Cyber intrusions into networks connected to electric grid OT networks allow an adversary to collect information, credentials, and find paths into systems that are responsible for the generation and transmission of safe and reliable power. Many policy makers believe that it is only a matter of time before the U.S. experiences an attack resulting in material damage. According to a survey from Pew Research, experts predict a major cyber attack between now and 2025 that results in property losses, damage, and theft of tens of billions of dollars. The Sony Pictures cyber attack has prompted many to take such predictions more seriously.
Actual Cyber Attacks on Critical Infrastructure
Cyber attacks on industrial and critical infrastructure have gone from potential to actual. A German federal agency reported that a steel mill’s operations were affected by a cyber attack in late 2014 that caused physical damage to a furnace. Attackers reportedly gained access to the steel plant’s network through a malicious email, which resulted in a breach to the plant’s control systems, causing physical damage. The attackers were then able to get into the production network and gain control over the furnace operations. Although it is rare that a cyber attack would cause physical damage to a plant, we are beginning to witness the progression of ICS-capable attacks.
More recently, South Korea reported a cyber attack against the operator of its nuclear power plants. Media reports are painting the picture that an unknown adversary used email addresses of retired employees to deliver malware, which reached systems connected to the ICS, throughout the company’s network. The attackers released sensitive and confidential information, including the plant equipment’s designs and manuals, online and through social media. South Korea claims that multiple IP addresses of the suspected hacker traced back to a northeastern city in China.
In years past, threats to power and utility companies were the result of technical vulnerabilities and human errors. Current threats are much different. They are customized, targeted, and involve campaigns to intrude upon production systems. Motivations for hacking into ICSs vary, but the ability to infiltrate, study, and control operations could lead to damage affecting more than the infrastructure operator.
China, for example, is very interested in U.S. business strategies, process, and practices. Gaining access to confidential information provides insight into the selection of suppliers, or what motivates businesses to make investments. Other attacks could involve extortion, nation states hacktivism, or leverage to be used in geopolitics. The results of these targeted attacks will certainly cause hardships to customers, damage reputations, undermine confidence, and renew concern for reliability.
Cybersecurity Regulations in the Power Industry
The transition from standalone to interconnected systems has gained significant traction over the past 10 years and, due to the potential implications, the U.S. government has gotten involved.
The Energy Policy Act of 2005 strengthened the Federal Energy Regulatory Commission’s (FERC’s) tools for protecting consumers from exploitation and developed stronger energy reliability. The policy gave FERC the authority to oversee the reliability of the nation’s bulk power system and to fine a regulated entity up to $1 million per day per violation of any FERC rule. Under this new regulatory system the North American Electric Reliability Corp. (NERC), named the nation’s Electric Reliability Organization by FERC, implemented Critical Infrastructure Protection (CIP) cybersecurity reliability standards.
The National Institute of Standards and Technology (NIST) also has played a role by releasing a Framework for Improving Critical Infrastructure Cybersecurity, a voluntary program to promote the protection of critical infrastructure. (See “NIST Cybersecurity Framework Aims to Improve Critical Infrastructure” in the February 2014 issue of POWER.)
Most recently, the U.S. House of Representatives passed the National Cybersecurity and Critical Infrastructure Protection Act of 2014 (Cyber Act), in an effort to protect the country against high-impact/low-frequency risks such as electromagnetic pulse weapons. The Senate, however, did not pass the Cyber Act, which would force the government to make plans to prevent and recover from large-scale blackouts. The act would encourage information sharing about cyber attacks between the DHS and private companies. Congress plans to try to move the bill forward again in 2015. In the meantime, every sector in the U.S. critical infrastructure must do what it can to protect itself.
The power industry remains vulnerable to cyber attacks as technology advances and attackers become more skilled in exploiting OT. “Our electric grid is a key target to exploit not only for its inherent vulnerability, but because we are so vitally dependent on it,” said Rep. Trent Franks (R-Ariz.), lead sponsor of the Cyber Act. Complying with regulations is certainly a step in the right direction, but there are additional proactive measures that ICS owners and operators should take to enhance their cyber protection.
Beyond Regulation: Better Power Industry Training Needed
The government has put many policies in place in order to protect infrastructures from cyber attacks. However, it takes years for bills to be written and legislation to pass, and attackers will not wait for government to issue regulations. So security professionals in power and utility companies should consider the intent of the regulations and apply measures and monitoring processes that go beyond what is strictly required by regulation.
Cyber threats are becoming more targeted and consequential, and the workforce in critical infrastructure is undertrained to address these types of threats. According to the SANS Institute, about 10,000 employees in the power industry need to be trained on how to defend against cyber attacks. These attacks are complicated, and vulnerabilities are constantly being discovered, so it is vital that engineers who are responsible for control systems are cross-trained with cybersecurity specialists for cyber threat detection, mitigation, and response.
As Adm. Rogers recently said, “being on the defensive is a losing strategy,” and the industry needs to realize the importance of working across disciplines to address the challenges that accompany positive advancements in OT.
It is wise to assume that an attacker will gain access to any device or network that connects to another network, and these considerations should be included in an organization’s incident response preparations. In addition, system operators should develop security capabilities for all of their facilities that support or are involved in infrastructure operations, not just systems and assets that are federally regulated.
Power companies need to create a comprehensive security strategy to keep up with the connected world we live in. That strategy must not only address physical security concerns and establish cyber perimeters. When considering targeted cyber attacks, always assume the attacker will gain a difficult-to-detect foothold on any device or network that has connectivity to the Internet or an accessible wireless signal. The interconnection of systems and introduction of new digital components create cyber attack surfaces that must be accounted for in system designs and cybersecurity strategies and plans.
Energy OT has purposeful and thus predictable communication profiles, and defenders need to leverage this important difference between OT and IT systems. Our collective challenge is to develop security capabilities and push them deeper into our operations and production systems. If a company wants to achieve the benefits of digital technology, it also needs to ensure that its systems operate well and with integrity. ■
—Michael Assante ([email protected]) is co-founder and chief security strategist of NexDefense. He serves on the board for the Council on Cybersecurity and is the ICS & SCADA lead for the SANS Institute. Previous positions include vice president and chief security officer at NERC and vice president and chief security officer for American Electric Power.
