Modern predictive maintenance depends on sensors and data streams that double as attack surfaces. Protecting the grid now means treating cybersecurity as a reliability discipline.
In the interconnected age of 2026 and beyond, reliability in power generation goes far beyond keeping a plant running. For more than a century, the primary focus of plant operators was the mechanical integrity of the assets, ensuring that turbines, boilers, and transformers were physically sound. Today, the rise of sophisticated sensors and cloud-based predictive maintenance has created a new reality where the mechanical health of a plant is inextricably linked to its digital security. While these advanced monitoring tools are essential for preventing unplanned outages, they also serve as a potential entry point for external threats. In this environment, a sensor is no longer just a diagnostic tool but a front door into the heart of the control system.
The Physical Reality of Digital Vulnerability
The primary goal of cybersecurity in an operational technology environment is not the protection of data privacy but the protection of the physical infrastructure itself. When a digital system is used to control high-energy machinery, a breach can lead to the hijacking or weaponization of those assets.
 |
|
1. Ransomware and state-sponsored intrusions targeting critical infrastructure have become an increasing threat to power plant and grid operators worldwide. Courtesy: Life Cycle Engineering / Adobe Stock |
This is not a theoretical concern. As a test in 2007, the Department of Homeland Security orchestrated a cyberattack on a 27-ton generator. The operation took control of the generator and opened its circuit breakers, ultimately resulting in a catastrophic failure captured on video. The so-called Aurora experiment took place in a controlled environment and did not affect a real power grid or actual plant employees, but it did prove risks can come very far from a plant’s physical location. Outside of experiments and research, there have been multiple real-world incidents where grid systems were held for ransom (Figure 1) or sabotaged by foreign actors including incidents in Romania and Poland in 2025.
In these scenarios, the loss of power isn’t just a technical failure, it’s a public safety crisis. Whether it is a grid hijacking during a cold winter or the recent sabotage of substations, the intersection of cybersecurity and reliability is now a matter of national security.
Calculating the High Price of Silence
The financial implications of an unplanned outage are staggering and serve as a clear business case for integrating security into maintenance workflows. According to a 2023 report by ABB Global, power generation facilities lost nearly $180,000 per hour of unscheduled downtime. For large baseload facilities, such as nuclear, coal, or gas combined cycle plants, these costs can be much higher, easily reaching $1 million for a day offline. These figures account for lost revenue, the high price of emergency procurement, and the labor required to restore operations.
When a cybersecurity threat is the cause of the outage, the costs can escalate further. According to IBM, the average cost of a data breach in the operational technology sector is more than $4 million, but the ripple effects often reach much higher. One can look at the impact of major pipeline disruptions, where a relatively small ransom payment led to more than a billion dollars in downstream economic damage. For power generation leaders, these numbers prove that cybersecurity is a fundamental component of the balance sheet and a necessary investment for long-term viability.
Navigating the Friction Between IT and OT
One of the greatest challenges to securing the grid is the cultural divide and competing priorities between information technology (IT) security teams and operational technology (OT) engineers. Engineers are focused on uptime and are frequently skeptical of any security protocols that might interfere with continuous operation. This apprehension is often based on past experiences where generic IT security practices caused significant problems in the plant environment.
 |
|
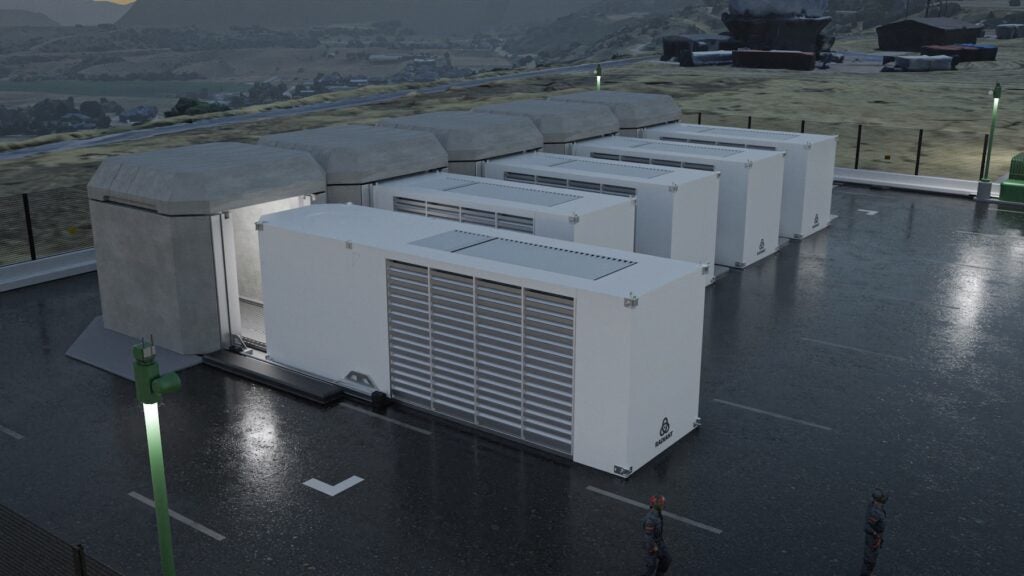
2. Effective operational technology security requires close collaboration with plant engineers who understand the operational constraints of installed machinery. Courtesy: Life Cycle Engineering / Adobe Stock |
For example, standard active security scans used by IT departments can have unintended consequences when applied to sensitive industrial hardware. There have been instances where a simple scan caused mission-critical machinery control systems or even industrial printers to stop functioning permanently. To overcome this friction, security professionals must move away from pushing pre-packaged solutions and instead focus on listening to the engineers who understand the specific limitations of their equipment (Figure 2). Effective security is built on environmental knowledge and a willingness to tailor protocols to the unique needs of the power plant.
Designing for Real World Resilience
Moving beyond a simple compliance mindset requires a strategic approach to asset management and network design. A facility cannot protect what it does not know it has, making a comprehensive inventory of all network-connected devices the first step in any security plan. This is especially critical for meeting North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) standards, which require the categorization of all assets. Many facilities suffer from blind spots where legacy hardware or secondary sensors remain unmonitored, creating vulnerabilities that attackers can exploit.
Once the assets are identified, the focus must shift to network segmentation. By moving away from flat networks and adopting models that silo different parts of the control system, operators can ensure that a breach in one area does not allow an attacker to gain access to the entire facility.
Another key concept is the use of compensated controls. In high-stakes environments, it is not always practical to use standard digital security methods, such as complex passwords, on consoles that must be accessed immediately during an emergency. In these cases, the intent of the security requirement can be met through alternative means, such as physical guards or secondary procedural controls.
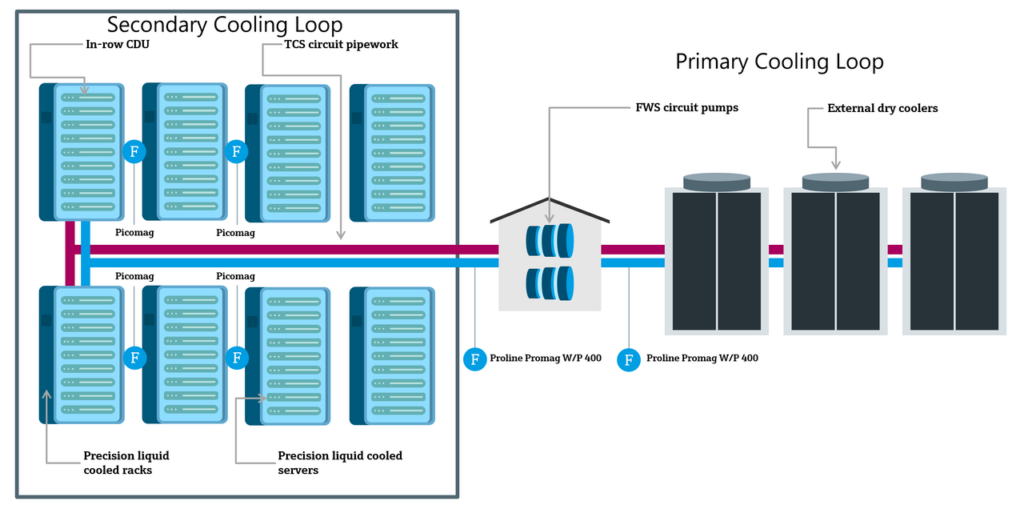
Artificial Intelligence as a Bridge and a Risk
The adoption of artificial intelligence (AI) and advanced predictive analytics is beginning to change the relationship between IT and OT personnel. Because both groups are now focused on leveraging data to improve plant health, they are finding more common ground (Figure 3). Engineers are increasingly looking to IT experts to help them manage and interpret the massive amounts of data generated by modern sensors. This collaboration is helping to break down traditional silos and foster a more unified approach to reliability.
 |
|
3. Information technology and operational technology professionals are finding the adoption of artificial intelligence and predictive analytics is creating shared objectives that help bridge the traditional divide between these two groups. Courtesy: Life Cycle Engineering / Adobe Stock |
However, the use of AI also introduces new risks that must be managed. One significant concern is the possibility of AI hallucinations, where the system makes incorrect assumptions based on bad or manipulated data. If a sensor is compromised and begins feeding false information into a predictive model, the AI could provide a faulty assessment of equipment health. This could lead operators to ignore a genuine mechanical problem or perform unnecessary maintenance that introduces new risks. To ensure that AI remains a tool for reliability, the integrity of the data it relies on must be protected with the same rigor as the physical plant hardware.
A Unified Path Forward
Reliability in the modern power generation industry can no longer be achieved through mechanical maintenance alone. It requires a proactive, integrated strategy that treats cybersecurity as a core component of plant operations. By understanding the physical and financial risks, bridging the gap between IT and OT cultures, and maintaining a focus on data integrity, generation professionals can protect their facilities from the evolving threats of the digital age. The future of the grid depends on the ability to secure every asset, from the most powerful turbine down to the smallest sensor.
—Randy Heisler is the vice president of Power Generation, and Michael Hoyt is the vice president of Enterprise IT Solutions at Life Cycle Engineering, a leading consulting company specializing in operational excellence, asset management, reliability and predictive maintenance strategies, and engineering solutions.