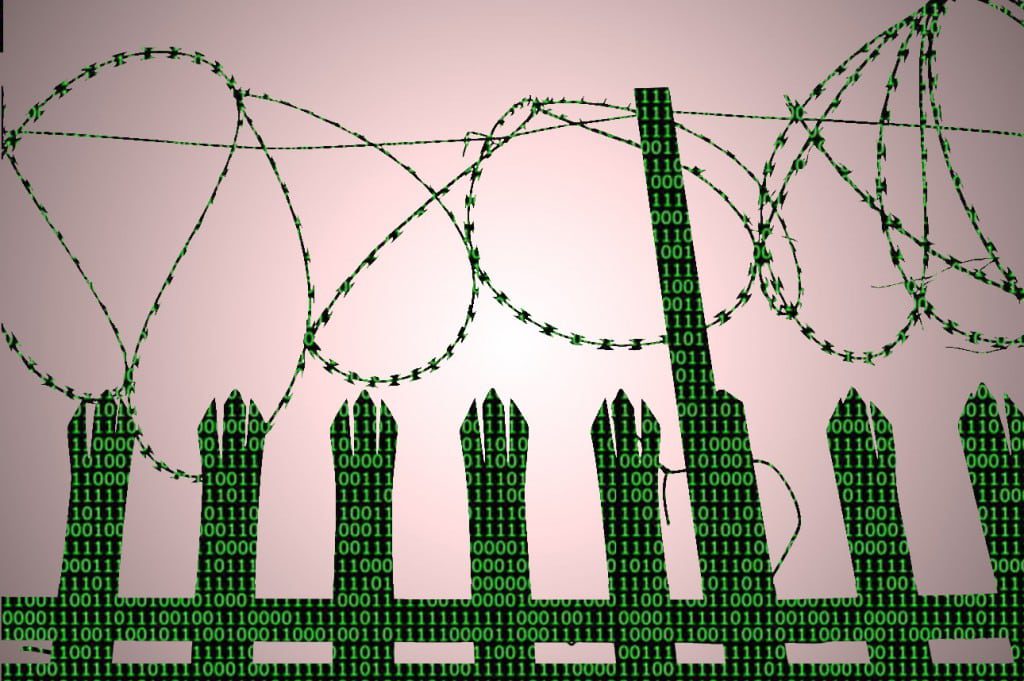
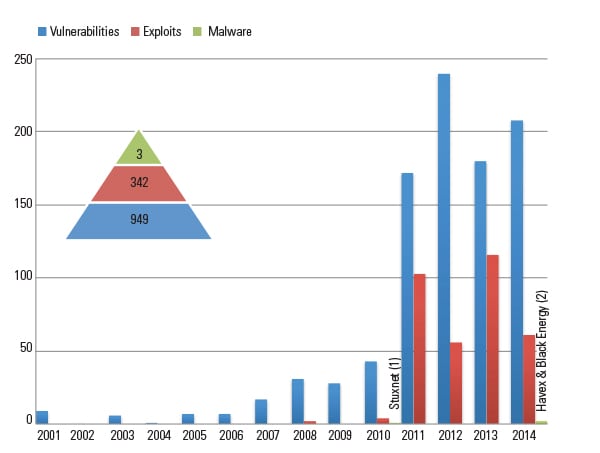
Cybersecurity threats facing the power industry have escalated dramatically in the past few years, as state-sponsored, organized crime, and hacktivist groups all seek to infiltrate U.S. energy infrastructure for cyber-espionage and sabotage purposes. A recent example of the severity of this threat can be seen in operation “Energetic Bear”—a Russian campaign to infect U.S. and Western European energy firms’ industrial control networks with remote access trojans.
The problem for U.S. energy firms, however, is that industrial control systems (ICS) are inherently vulnerable and hard to defend. Protecting these critical networks from exploitation requires a multi-layered security approach that involves physical controls, a highly trained security team, intrusion detection/prevention systems (IDS/IPS), anti-malware scanners, firewalls, security information and event management (SIEM), and more.
But the reality is, not even all of that is enough. Each of these tools—as well as the human team managing them—has key limitations, which can prove disastrous when combating an advanced and persistent adversary such as a state-sponsored hacking group. Some of these limitations include: a high rate of false positives, which slow down the security team; inability to detect new or custom-made malware; trouble blocking internal-based threats; and response geared toward threats in the network, rather than before they impact the network.
Here are a few examples of how these limitations can undermine a security program:
- Target Corp. In November and December of 2013, Target fell victim to a massive data breach of its point-of-sale systems from the BlackPOS malware. The company’s anti-malware detection system actually caught the threat early on, but Target’s security team ignored the warnings.
- Iranian Oil Ministry. In April and May 2012, Iran’s Oil Ministry was infected by the Flame malware, widely believed to be the most advanced malware ever discovered at that time. This malware was designed to detect a company’s antivirus settings and change its behavior to avoid detection. It was also able to avoid detection from various security tools as it spread throughout the network and exfiltrated data.
- Iranian Nuclear Program. In 2010, Iran’s nuclear program was attacked by the Stuxnet computer worm, which caused physical damage to its machinery. The worm used four software vulnerabilities (then unknown to the world) to target computers, software, and industrial systems.
So what is the solution?
The Honeypot
The most effective way for energy firms to overcome these obstacles and harden their defenses against nation-state threats is by deploying a tool known as the “honeypot.”
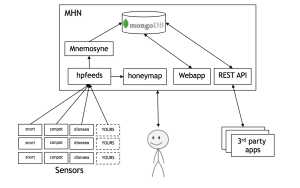
A honeypot is basically just a dummy network node, software application, or computer that exists for the sole purpose of getting hacked (Figure 1). To the attacker, the honeypot looks like a real computer network that is poorly protected; in reality, it’s a fake system that is isolated from the rest of the organization’s network and monitored closely by a security team and automated tools.
A honeypot can be made to look like any number of things that would entice a hacker, including a desktop computer, web application, back-end server, USB thumb drive, or database. Its job is basically to act as bait for hackers and malware, luring them into the dummy system in order to detect what threats are targeting the network. Honeypots are generally a very low-cost security solution as well, since there are numerous open source tools available.
Because of the way honeypots are designed and how they interact with hackers and malware, they can aid energy companies in several key ways:
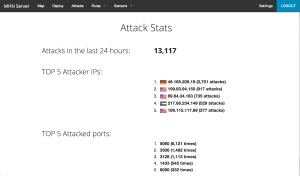
- Serve as an Early Warning System. Honeypots are often the first to be attacked, because they look like weak, vulnerable points on a network to an attacker. This makes them an effective “early warning system” for a company because they identify active threats before these impact the real network, giving the security team time to prepare. When integrated with other security tools (like IDS/IPS, SIEM, firewalls, and anti-malware), this early warning system can dramatically improve a company’s other security layers by feeding them valuable intel on pending attacks so that each security tool is ready for them.
- Catch New Malware. Anti-malware scanners don’t always detect new viruses, trojans, and worms. That’s because hackers often test their malware against widely used scanners to make sure it will avoid detection before they release it into the wild. A honeypot is different though. Because it’s basically just a dummy network, there should be no activity on it at all. Therefore, any anomaly is quickly identified. This allows it to catch and report otherwise undetectable malware.
- Detect “Zero-Day” Exploits. Zero-days are software vulnerabilities that no one knows about yet. As such, they’re extremely hard to defend against. A good example is the Stuxnet worm, which utilized four zero-days when infiltrating Iran’s nuclear program. “High-interaction” honeypots can be used to identify zero-day attacks, since they run operating systems, software, and the like in an insecure environment.
- Detect Insider Threats. When attacks are made from behind the firewall, using legitimate account credentials and a company’s own IP address, they can be difficult for many security tools to spot as malicious. Again, honeypots make the difference, because if anyone is accessing its fake environment, the activity is by rule malicious.
- Streamline Threats. Many security tools are “noisy,” in that they issue frequent alerts, with no clear distinction between high- and low-level threats, and are plagued by many false alarms. This makes it difficult for a security team to prioritize threat warnings and can even lead to some security personnel becoming jaded and ignoring alerts, as was the case in the Target breach. Honeypots can improve this process because they have very few false-positives. That means any alerts issued by them are known to be real, which helps security teams triage better, verify other threat intel, and respond more quickly.
- Confuse Attackers. If an attacker does get into the organization’s network, a honeypot can be used to slow him down. When laden with decoys, a honeypot will confuse and distract an attacker, taking his time away from finding the real data or network point he’s looking for, and giving the security team more time to respond.
Overcoming Obstacles to Using Honeypots
The many advantages of honeypots have been well-known for over 20 years, but they’ve never been widely used within the energy industry. The reasons include lack of awareness, technical difficulties, and misconceptions. With that in mind, let’s take a look at the “problems” with honeypots.
Honeypots Are Difficult to Deploy/Manage. Many organizations see honeypots as too complicated to launch and manage over time, and view them primarily as a tool for security researchers. While it is true that there is some technical complexity involved with setting up a honeypot, this is a challenge that any energy firm should be able to overcome by utilizing free open source tools, undergoing specialized training, and/or consulting with a third-party security firm.
Additionally, although it’s recommended that energy firms deploy a diverse, widely distributed honeypot network to better cover their networks and support their security tools, some organizations have also opted to deploy the simplest of all honeypots—old computers scheduled for recycling that are instead repurposed as dummy machines and set aside on the network to look for malicious activity. A honeypot network can be as big or small, sophisticated or simple, as the organization wants (Figure 2).
Honeypots Expose Your Organization to Greater Risk. There are some IT professionals who believe that honeypots, by their very nature as hacker targets, will expose an organization to undue risk. While it is true that some types of honeypots are riskier than others, it’s important for energy firms to understand that this is not the case when done right.
For this discussion, there are two types of honeypots to consider: “high-interaction” and “low-interaction.” A high-interaction honeypot does have greater risks, as it uses a real operating system or software application for the hacker to target. This type of honeypot can be used with great success, but it requires a higher degree of security controls and human oversight to prevent possible threats. Because of these additional requirements, it’s best to avoid high-interaction honeypots and use low-interaction ones instead. A low-interaction honeypot doesn’t use a real operating system, application, or other exploitable surface, which makes it very low-risk to use and much easier to deploy and manage.
How to Use Honeypots
For energy firms and other industrial users, here are a few things to consider when deploying a honeypot:
- Protect Enterprise and ICS Networks. In order to be effective, energy companies should deploy low-interaction honeypots on both their enterprise networks and ICS networks. These two sets of honeypots should be kept separate (with no shared systems or resources) and the ICS honeypots should be extremely locked down to prevent any potential risks.
- Deploy on Both Inside and Outside Firewalls. By deploying honeypots inside the firewall (both for enterprise and ICS), the organization will be able to set up an effective early warning system that can be used to spot advanced threats. Honeypots deployed inside the firewall are meant to detect compromised devices inside the network. These honeypots should have no legitimate traffic going to them, so any traffic targeting these devices should be considered suspect and will likely lead to a compromised or misbehaving device.
- Build a Diverse Network. Use multiple honeypots of different varieties (simulated operating systems, workstations, software applications, servers, and so on). Building in variety helps avoid the honeypots being easily detected, fingerprinted, or avoided.
- Integrate with Other Security Tools. Honeypot log events should be fed into existing security products and SIEMS.
- Use Open Source Tools. There are a number of open source tools available for deploying honeypots, including Conpot, Dionaea, and Kippo.
- Train. Organizations should also consider industry training, such as SANS and Black Hat, to learn about honeypots.
Energy companies really should take a serious look at how they can begin to implement a distributed honeypot network within their current security programs. Cyber attacks on this industry will continue to escalate for some time, as it represents a key target in cyber warfare scenarios that almost every country is currently developing. Although today’s energy firms may be aware of the espionage threats posed by China and Russia (and these should not be underestimated), it must also be understood how real the risk is of future sabotage and physically destructive attacks. The energy industry must take proactive measures now to enhance its capabilities against these sophisticated threats. Honeypots should form a key part of that defense strategy.
—Greg Martin is founder and CTO of ThreatStream, a Google Ventures–backed cyber threat intelligence firm that provides services to a wide range of U.S. industries, including defense, tech, critical infrastructure, and finance. Greg is a former technical advisor to the FBI, Secret Service, and NASA.