On April 7, Anthropic announced Project Glasswing, a coalition of 12 major technology companies marshaling a new frontier artificial intelligence (AI) model to find and fix critical software vulnerabilities before attackers can exploit them. While the announcement is framed around technology infrastructure broadly, the implications for the power sector are immediate and serious. Partner posts from Amazon Web Services (AWS), Cisco, CrowdStrike, Microsoft, Palo Alto Networks, and the Linux Foundation reinforce the urgency—and offer concrete detail on what has changed. Here’s what energy leaders should take away and what to do about it.
The Headline: AI Can Now Find Vulnerabilities Faster Than Humans Can Patch Them
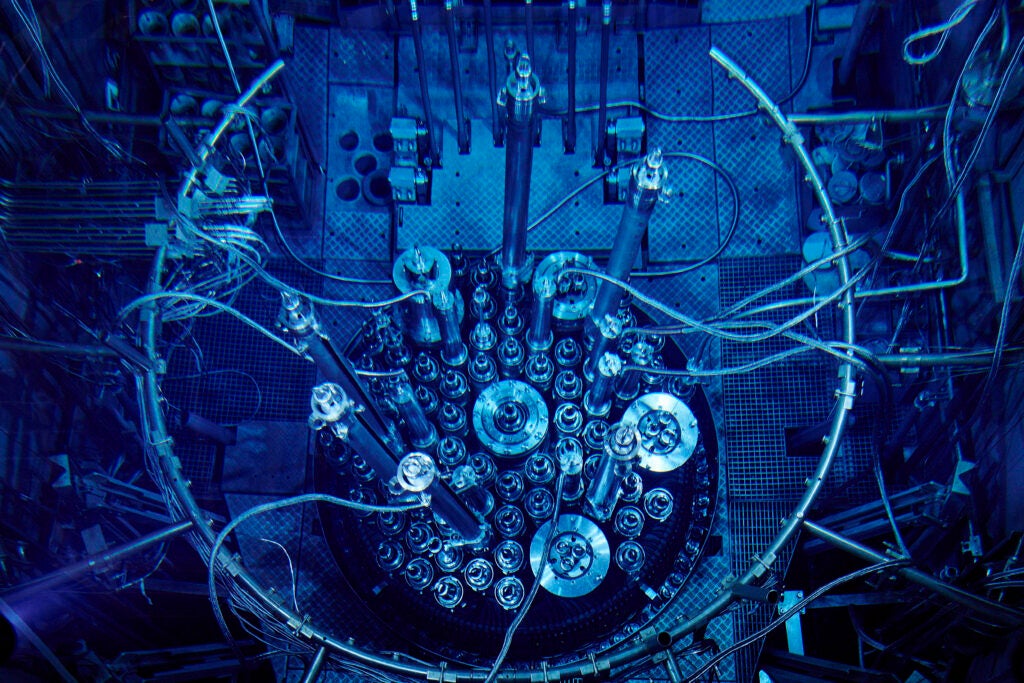
Anthropic’s unreleased Claude Mythos Preview model has already discovered thousands of previously unknown zero-day vulnerabilities across every major operating system and browser. One flaw it found had survived 27 years in OpenBSD, a system widely used to run firewalls and critical infrastructure. Another sat undetected in FFmpeg code that automated tools had tested five million times. The model also chained together multiple Linux kernel vulnerabilities to escalate from ordinary user access to full machine control, exactly the kind of attack path that could compromise a utility’s supervisory control and data acquisition (SCADA), distributed control system (DCS), or energy management system (EMS) environments.
The key takeaway isn’t just that this particular model is powerful. It’s that AI capability at this level will inevitably proliferate. As Palo Alto Networks CEO Nikesh Arora put it bluntly, within months a sophisticated attack capability will be “available to anyone with a credit card and compute.” For grid operators running decades-old control systems and embedded firmware, the window to prepare is shrinking fast.
What the Coalition Partners Are Reporting
The partner releases add critical context beyond Anthropic’s own announcement. Taken together, they paint a picture of a threat landscape that is already shifting faster than most organizations realize.
The Speed Gap Is Already Alarming
Palo Alto Networks reports that the fastest AI-assisted attacks are already moving from initial access to data exfiltration in just 25 minutes, while the average enterprise still takes days to detect an intrusion. For utilities with complex operational technology (OT) environments and multi-day patching cycles, that mismatch is existential.
AI-Powered Defense Is Already Delivering Results at Scale
AWS reports that its AI-powered log analysis system has cut the time security engineers spend analyzing logs from an average of six hours down to seven minutes—a 50x productivity gain. AWS also analyzes more than 400 trillion network flows per day and blocked more than 300 million attempts to maliciously encrypt customer files on its S3 cloud storage platform (that is, Simple Storage Service) in 2025 alone. These numbers illustrate what AI-augmented defense looks like when deployed at scale, and AWS has set the benchmark utilities should be aspiring to.
Existing Logging Is Failing, Not Because It Doesn’t Exist, but Because It’s Fragmented
Palo Alto Networks cites research showing that in 75% of breaches, logging existed that should have flagged anomalous behavior, but critical signals were buried across fragmented tools and never acted on before it was too late. For utilities running separate monitoring stacks across information technology (IT), OT, and cloud environments, this finding should be a wake-up call.
AI-Assisted Attacks Are Surging
CrowdStrike’s 2026 Global Threat Report documents an 89% year-over-year increase in attacks by adversaries using AI. The threat is not hypothetical or on the horizon; it is already accelerating.
Vulnerability Discovery Is Becoming Continuous and Autonomous
Microsoft’s Security Response Center said AI is enabling vulnerability discovery around the clock, at a scale and speed that previous methods could not match. Microsoft is embedding AI-driven red teaming directly into its software development process so issues are caught as code is written. Cisco reports that AI-powered analysis is uncovering vulnerabilities at a depth that legacy security frameworks were never designed to handle.
AI Can Now Help Patch What It Finds
The Linux Foundation’s Jim Zemlin noted that Claude Mythos Preview and similar models are not only identifying vulnerabilities but also generating viable patches. Linux kernel maintainer Greg Kroah-Hartman, initially skeptical, has acknowledged that some AI-generated patches have been of good quality. For power-sector software where patches have historically required months of vendor coordination, AI-assisted patching could dramatically compress remediation timelines.
Why This Matters Disproportionately for the Power Sector
Power grids sit at the intersection of several risk factors that make these developments especially relevant. No single factor is unique to the energy sector, but the combination creates a level of exposure that few other industries face.
Legacy Software Is Everywhere
Substations, SCADA systems, and energy management platforms routinely run on software that was written years or decades ago. Many of these systems were designed before cybersecurity was a primary concern. If an AI model can find a 27-year-old flaw in one of the most security-hardened operating systems in the world, it can very likely find exploitable weaknesses in aging utility control systems.
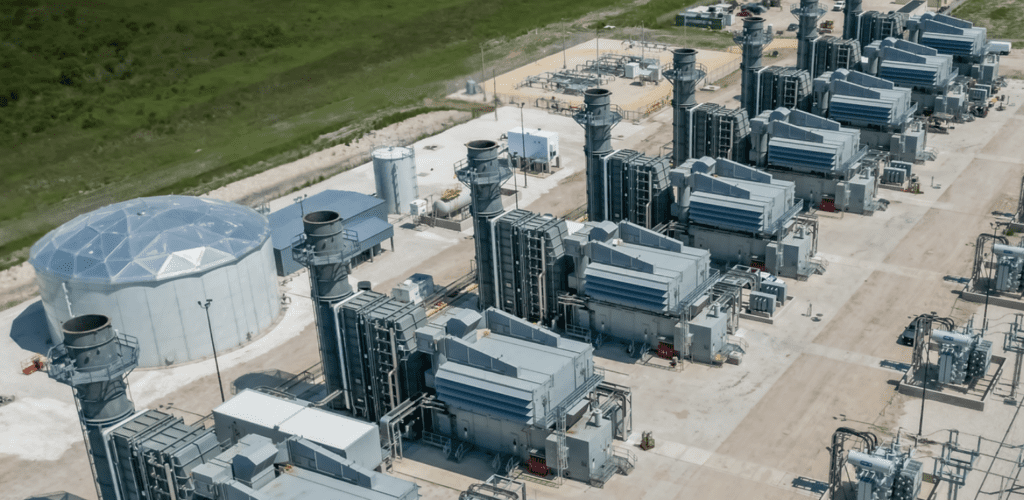
OT Is Increasingly Networked
The push toward grid modernization, distributed energy resources, and cloud-connected analytics has dramatically expanded the attack surface. Every new smart inverter protocol, distributed energy resource management system (DERMS), and advanced metering infrastructure (AMI) network adds code that could harbor latent vulnerabilities. Arora warned that the average company already relies on thousands of vendors and millions of open-source dependencies with years of accumulated exposure—configuration errors, overlooked API (application programming interface) endpoints, access policies that once made sense and were never revisited. Utilities are no exception.
Shadow AI May Already Be on Networks
CrowdStrike said it discovered more than 1,800 AI applications running across its customer environments, many of them deployed without security team approval. Employees across utilities are experimenting with AI tools and agents that may be operating near sensitive systems without governance. Every desktop now effectively behaves like a server, and if unsupervised AI tools are running near OT networks, the risk is compounding silently.
Consequences Are Physical, Not Just Financial
A compromised banking system loses money; a compromised grid loses power. The 2015 and 2016 cyberattacks on Ukraine’s grid demonstrated that adversaries can and will target energy infrastructure to cause real-world outages. AI-augmented attackers will be able to do so faster and at greater scale. With access-to-exfiltration times already measured in minutes, a well-targeted attack on grid control systems could cause physical damage before operators are even aware of the intrusion.
Patching Cycles Are Slow
Unlike consumer software that updates overnight, OT in substations and generation facilities often can’t be patched without planned outages, vendor coordination, and regulatory approval. The gap between vulnerability discovery and patch deployment is measured in months or years, a timeline that AI-powered attackers will ruthlessly exploit.
Actionable Steps for Power Companies and Grid Operators
The vulnerabilities are real and the time to act is short. Here are eight actions power companies and grid operators should take today.
1. Inventory Software Attack Surfaces
If you don’t have a comprehensive, current catalog of every piece of software running in both your IT and OT environments—including firmware versions, third-party libraries, and open-source dependencies—build one. You cannot defend what you cannot see. CrowdStrike’s finding that more than 1,800 unauthorized AI applications are running across typical enterprise environments underscores that the inventory problem extends beyond traditional software to AI tools and agents that employees are adopting on their own. Prioritize systems that bridge IT and OT networks, since these are the most likely entry points for escalation attacks like the Linux kernel chain Mythos Preview demonstrated.
2. Consolidate Security Monitoring
Fragmentation is a critical risk. Palo Alto Networks’ data showing that three-quarters of breaches had logging that should have caught the attack—but the signals were buried across disconnected tools—is directly applicable to the power sector. Many utilities run separate monitoring for IT networks, OT/SCADA systems, physical security, and cloud environments. When attacks move at AI speed, signals scattered across siloed dashboards will not be correlated fast enough. Consolidating security data into a unified platform is no longer a modernization preference; it is a prerequisite for survival against AI-enabled threats.
3. Engage with Project Glasswing and Its Outputs
Anthropic has committed to publishing lessons learned and practical security recommendations within 90 days. The coalition will also produce guidance on vulnerability disclosure, patching automation, supply-chain security, and standards for regulated industries. Grid operators and utilities should designate staff to monitor these publications and feed them directly into their security programs. If your organization maintains open-source software used in energy systems, apply for access through the Claude for Open Source Program—the Linux Foundation is working to ensure maintainers of critical open-source infrastructure get free access to these tools.
4. Accelerate Patching and Update Processes
With AI-assisted attacks already achieving access-to-exfiltration in 25 minutes while enterprises take days to detect intrusions, the window between vulnerability discovery and exploitation has effectively collapsed. Utilities need to revisit their patch management timelines and push hard to shorten them, especially for internet-facing systems and any software that touches grid control. The emerging AI capability to not only find vulnerabilities but also generate patches should be evaluated as a way to compress the remediation cycle. Where immediate patching isn’t feasible, deploy compensating controls such as network segmentation, application whitelisting, and enhanced monitoring.
5. Pressure Vendors
Much of the software running critical grid infrastructure is maintained by third-party vendors. Cisco’s acknowledgment that AI-powered analysis is revealing vulnerabilities that legacy security frameworks were never designed to accommodate should prompt utilities to ask hard questions of their EMS, SCADA, DCS, and DERMS vendors: Are you using AI-powered vulnerability scanning on your products? What is your patch response timeline? Are you participating in or tracking Project Glasswing’s findings? Microsoft’s move to embed AI-driven red teaming directly into its development lifecycle should become the standard you expect from every vendor touching your grid.
6. Adopt AI-Powered Defensive Tools
If attackers will have AI working for them, defenders need it too. AWS’s demonstration of a 50x productivity improvement in security log analysis shows the kind of force multiplication that is possible. Palo Alto Networks’ framework offers a useful mental model for utilities: you need sensors across network, cloud, and endpoints to collect data; an AI-enabled data lake to provide context and convert noise into actionable intelligence; and a consolidated platform that eliminates the silos that currently bury critical signals. Evaluate AI-driven security tools for vulnerability scanning, anomaly detection, and automated threat response across both IT and OT environments.
7. Prepare for the Regulatory Wave
North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) standards provide a regulatory floor, not a ceiling. The threat environment described across these announcements suggests that compliance alone is insufficient. Additionally, CrowdStrike noted that the next phase of the European Union (EU) AI Act takes effect on Aug. 2, 2026, introducing automated audit trail requirements, cybersecurity mandates for high-risk AI systems, incident reporting obligations, and penalties up to 3% of global revenue. While the EU AI Act applies most directly to European operations, it signals the regulatory direction globally. Utilities should benchmark their security programs against both the forthcoming Glasswing recommendations and emerging AI governance requirements, and treat them as the new standard of care.
8. Plan for the Workforce Gap
AI-augmented cybersecurity will require people who understand both power systems and modern security practices. Begin cross-training grid engineers on cybersecurity fundamentals and security staff on OT protocols. The Linux Foundation’s core argument applies directly to the power sector: security expertise has historically been a luxury that smaller utilities and open-source maintainers can’t afford, and AI tools can help democratize access to advanced security capabilities. Position your teams to use these tools effectively as they become available.
Defensive Collaboration Is Crucial, but the Risk Curve Has Already Changed
Project Glasswing is a warning dressed as a solution. The coalition is doing important defensive work, but the underlying message—reinforced by every partner post—is stark: AI has crossed a threshold that permanently changes the cybersecurity landscape for critical infrastructure.
The numbers tell the story. Attacks moving from access to exfiltration in 25 minutes. An 89% year-over-year increase in AI-assisted attacks. Three-quarters of breaches with logging that should have caught them but didn’t because the data was fragmented. These are not future projections; they are current conditions, and frontier AI models will make every one of them worse.
Power companies that treat this as someone else’s problem, or as a challenge they can address on legacy timelines, are accepting a level of risk that is no longer tenable. The companies and agencies that move first to harden their systems, consolidate their monitoring, demand more from their vendors, and integrate AI-driven defense into their operations will be the ones best positioned when these capabilities inevitably reach hostile actors. The time to start is not after the next grid-targeted attack. It is now.
—Aaron Larson is executive editor of POWER.