EPRI and Luminant Collaborate to Create Common Understanding of Cybersecurity Requirements
A collaborative effort between the Electric Power Research Institute and the Comanche Peak Nuclear Power Plant confirms that vendors and nuclear plant owners who understand and address cybersecurity requirements up front will avoid costs on the back end. The best practices developed also apply to non-nuclear plants.
Nuclear utilities are facing stringent cybersecurity requirements for plant digital assets that fulfill safety-related, important-to-safety, security, and emergency preparedness functions or that are associated with continuity of power. Such requirements are intended to protect plant digital computer systems, communications systems, and networks from cyber attacks that could affect reactor safety or generation reliability.
Determining the applicable cybersecurity requirements and factoring these requirements into modifications at project inception will avoid costly redesigns and rework.
In addition, nuclear plant owners must consider cybersecurity requirements throughout the life cycle of a plant digital asset and account for these requirements during the design phase. The Electric Power Research Institute (EPRI) has collaborated with Luminant and other nuclear utilities to help suppliers understand exactly what utilities need to establish effective cybersecurity requirements, and also to provide utility engineers with the technical guidance needed to meet those requirements by properly implementing the right vendor solutions.
EPRI has issued two key guideline documents aimed at improving the way all power generation plants, not just nuclear power facilities, tackle cybersecurity challenges: Cyber Security Procurement Methodology (Product 3002001824) and Technical Guideline for Cyber Security Requirements and Life Cycle Implementation Guidelines for Nuclear Plant Digital Systems (Product 1019187). And although control system cybersecurity technology will evolve over time, cybersecurity requirements largely will remain the same, which means the approaches defined in these guidelines are expected to provide a dependable, standard approach to cybersecurity that will last over time.
Luminant implemented the guidance from both documents at its Comanche Peak Nuclear Power Plant in Texas by early 2013. Using the guidance to clearly interpret the nuclear industry’s cybersecurity procurement controls and integrate them into purchase specifications and contracts, Luminant expects to save more than $600,000 in avoided cost overruns on digital system upgrade modifications for a plant computer replacement and a security system video capture at Comanche Peak.
Cybersecurity Requirements Ramp Up
Prior to 2001, plant digital systems included basic physical and information security requirements in specification and design documents. In general, however, these cybersecurity requirements were not based on information security industry standards. After Sept. 11, 2001, the U.S. Nuclear Regulatory Commission (NRC) and the Federal Energy Regulatory Commission (FERC) began issuing orders on the subject.
In March 2009, the NRC issued 10 CFR 73.54, which requires plants to provide assurance that the digital computer and communication systems and networks associated with the following functions are protected against cyber attacks: safety-related and important-to-safety functions; security functions; and emergency preparedness functions, including off-site communications. Support systems and equipment that would adversely affect these functions if compromised are also covered by this set of requirements.
Comanche Peak’s cybersecurity program also addresses cybersecurity requirements established through a memorandum of understanding between the NRC and the North American Electric Reliability Corp.
Guidance Throughout the Life Cycle
The Technical Guideline for Cyber Security Requirements and Life Cycle Implementation Guidelines for Nuclear Plant Digital Systems gives plant operators guidance on how to build cybersecurity into new critical digital assets. Written in a procedural format that can be immediately incorporated into a plant’s existing digital design control procedures, the guidelines cover 138 areas of security in detail—everything from passwords and wireless connections to encryption and intrusion detection.
The cybersecurity requirements and guidelines are structured according to the life cycles of digital instrumentation and control systems and equipment. In that way, the guidance not only provides engineers with what requirements need to be included in a requirements specification but also includes what engineers should look for during various phases of the design’s life cycle.
The document discusses the cybersecurity threats that plants face and the compliance standards for those plants. It contains two appendices. The first, based on Comanche Peak’s own procedures to avoid failure events, contains a checklist and a methodology to address technical and regulatory issues involving plant digital systems and devices regulated by the NRC. The checklist recommends steps to ensure cybersecurity in all life-cycle phases (Table 1).
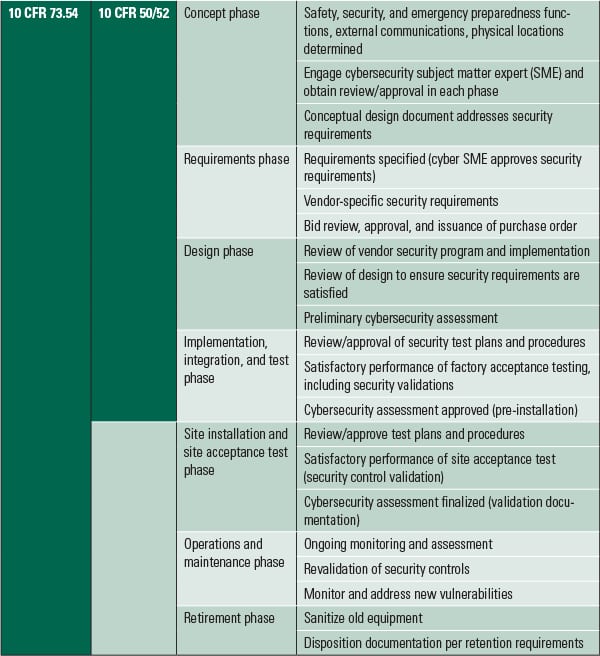 |
| Table 1. System development life cycle phases. Source: Luminant |
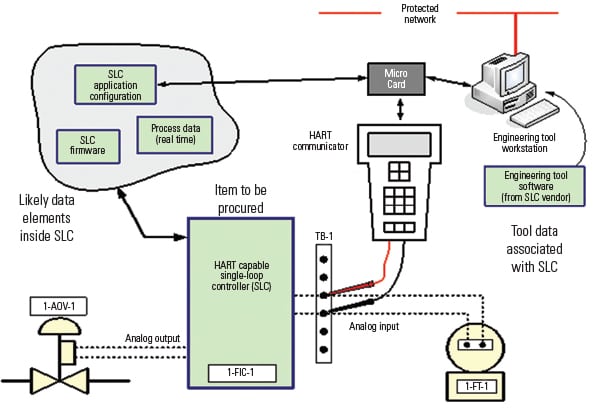
For example, during the conceptual phase, the design engineer determines if the modification contains digital assets, and what specific functions the digital assets will perform. The design engineer completes a form describing the digital features of the design. This form, and an accompanying simple network diagram, will facilitate a conversation with the station cybersecurity subject matter expert (SME) on required functions and cybersecurity features for the modification (Figure 1). Once the functions are defined, the design engineer and cybersecurity SME can determine the regulatory scope and treatment for the modification.
Once the regulatory scope is determined for NRC-regulated critical digital assets, the procedure contains instructions for completing a cybersecurity controls checklist to facilitate addressing the cybersecurity controls provided in Nuclear Energy Institute (NEI) 08-09 Revision 6, Appendix D (Technical Controls) and Appendix E (Operational and Management Controls) for the system development life cycle. (Note that NEI 08-09, Cyber Security Plan for Nuclear Power Reactors, is the U.S. nuclear industry document developed to assist licensees in constructing and implementing their Cyber Security Plan license submittal as required by 10 CFR 73.54.) The checklist provides entry cells for various pieces of data, including:
- Life-cycle guidance for the requirements, design, and post-design phases: This column contains specific guidance for addressing cybersecurity control for certain life-cycle phases. For example, some cybersecurity controls, such as network scanning, cannot be implemented directly into the design but take place in the operation and maintenance (O&M) phase.
- Requirements/specification references: A brief summary of the analysis addressing the cybersecurity control in the requirements life-cycle phase would be recorded in this column by the digital design engineer, along with requirements document references supporting the summary.
- Design references: A brief summary of the analysis addressing the cybersecurity control in the design life-cycle phase is recorded in this column by the digital design engineer, along with design document references supporting the summary.
- Test references: A brief summary of the analysis addressing the cybersecurity control in the testing or post-design life-cycle phases is recorded in this column by the digital design engineer, along with testing (factory acceptance test, site acceptance test, and so on) document references supporting the summary.
The second appendix shows the practical application of the procedures, using four examples drawn directly from actual plant modifications and reflecting real-life techniques that plant personnel would use on their equipment. The examples encompass a digital protective motor relay, a safety-related digital sequencer, a digital radiation monitoring system, and a turbine-generator digital controls system. The online version of this article includes a downloadable file that provides a portion of the completed cybersecurity controls checklist that Luminant completed for the digital protective motor relay.
EPRI also has developed a computer-based training module to train engineers working on modifications involving digital upgrades. Comanche Peak and several other nuclear plants have used this module to support cybersecurity training.
Improving Clarity
EPRI Report 1019187 also simplifies implementation of the security controls contained in NEI 08-09, Revision 6. Previously, there had been no guidance to help interpret the 600-plus requirements mentioned in the document, which cover areas such as procurement, contracts, vendor design, and in-house environments. Lacking guidance, some licensees had even postponed digital upgrades.
The EPRI guidance provides clear, specific requirements for critical digital assets so nuclear plant owners can target only those that pertain to them and the specific plant change they are making. It also helps vendors understand what each requirement stipulates. The clarity will help avoid technical misunderstandings and associated costs during subsequent design life-cycle phases.
For example, the requirements phase of the system development life cycle includes the following specific guidance for cybersecurity review activities as part of the design engineer review of vendor/contractor proposals/response to the procurement specification:
- Cybersecurity attributes for the digital modification provided in the procurement specification shall be addressed and documented by the design engineer.
- The cybersecurity SME (cybersecurity specialist) reviews and signs off on the vendor response to the procurement specification.
- The design engineer shall ensure that all vendor deviations/exceptions to requirements are addressed for security impact. The cybersecurity SME reviews and approves all vendor-proposed alternate controls. The cybersecurity SME shall identify where alternate controls will be used for cybersecurity and approve the preliminary vendor approach.
- The cybersecurity SME provides input into cybersecurity requirements for the vendor in the contract for items such as hold points reviews, vendor commitments, and milestones as they pertain to cybersecurity.
Cybersecurity Procurement Methodology
The guidance provided in the second EPRI document, Cyber Security Procurement Methodology, puts suppliers and nuclear plant owners on the same page so that both are familiar with the procurement and supply chain cybersecurity requirements and can avoid costly rework. In the past, differing interpretations of cybersecurity regulations often led to varying requirements for the same products. Suppliers also often didn’t know what role the nuclear plant owners expected them to play in providing cybersecurity.
EPRI research has shown that a standard set of cybersecurity control requirements with a standard set of procurement specifications is not feasible for the multitude of equipment types, vendors, and use cases that exist in the various types of facilities and applications. Consequently, a procurement methodology has been developed for determining the appropriate cybersecurity requirements for each use case as informed by a number of factors.
Many of the cybersecurity controls can be implemented only by the facility. Examples include incident response policy and procedures, and physical access authorizations.
In some cases, the supplier can provide the technology or feature to implement the cybersecurity control, but the utility actually implements the cybersecurity control. Examples include password requirements and baseline configuration. In these cases, the supplier provides the ability to create and manage passwords and a baseline configuration, but the owner should perform the actual management of passwords and maintain the critical asset baseline configuration.
In other cases, the supplier may be able to provide a security feature or function built into or added onto its product, but the owner may have already implemented a different technology or platform at the facility. An example could be audit reduction and report generation, as the owner may already have an audit log aggregation and reporting capability in a centralized security system. The requirement then would be for the supplier to provide the capability to transmit audit logs and records to the utility’s existing audit reporting system rather than use the supplier’s audit reporting system.
Cybersecurity requirements should be considered a subset of the larger set of design inputs and design outputs in the existing modification and design processes. Digital systems often have other critical requirements, such as response time and availability that could be negatively affected by a cybersecurity requirement (for example, encrypting data transmissions). These system-level functional and performance requirements should be considered in tandem with cybersecurity requirements. When combined, the full set of requirements helps determine not only which cybersecurity controls are required from a supplier but also how the cybersecurity control is implemented by the supplier.
To understand why a “one size fits all” cybersecurity specification is not practical, it is helpful to use a simple mechanical analogy. Safety-related pumps in nuclear facilities must be anchored to their foundations. It is not practical to write one specification that encompasses all of the characteristics of all of the bolts that may be used for anchoring all pumps. It depends on the size of the pump, its dynamic loading, its seismic loading, and other factors. However, it is helpful to have a methodology for routinely determining the necessary length, diameter, thread pitch, and material characteristics for bolts used to anchor pumps, so that the bolts can be specified and procured for each application in a predictable manner. Cybersecurity controls, in relation to critical digital assets, should be treated the same way.
The methods described in the report are based on the established owner/operator cybersecurity strategy, life-cycle processes, and roles and responsibilities. These elements are expected to be established, determined, or identified before procuring a critical asset.
The report provides guidance on what to do before communicating with the supplier, what to do when communicating with the supplier, how to evaluate supplier information, and how to go about procuring the digital asset. For example, the guidance defines specific outcomes that should be expected during and after communicating with the supplier:
- The supplier will identify and map supplier component cybersecurity capabilities to the security controls identified in the cybersecurity control table.
- The supplier will identify any deviations, exceptions, conflicts, or options.
- The supplier will provide documentation for all responses.
- The supplier will describe the supplier’s development environment and how development assets are protected.
Based on such evaluations, it is prudent for the plant owner to update the requirements specification to ensure the conformed requirements specification is issued with the supplier prior to issuance of the contract or as the first step toward contract execution to avoid costly rework or change in scope.
EPRI expects to have a computer-based training module on the procurement methodology available in 2014 to support procurement engineers, design engineers, and the vendors’ own in-house engineers.
Results from Comanche Peak
By using these guidelines developed in collaboration with EPRI, Luminant has been able to identify and solve problems early in the contracts phase, thereby avoiding cybersecurity-related missteps during the design phase that can cause increases in the scope and budget or create workarounds. For example, discussion with the supplier on the plant computer cybersecurity requirements resulted in bringing both parties to a common understanding, including issuance of a conformed requirements specification signed off by both the supplier and Luminant.
As mentioned earlier, Luminant expects to save more than $600,000 in avoided cost overruns on digital system upgrade modifications for the plant computer replacement and a security system video capture at Comanche Peak Nuclear Power Plant.
For the plant computer replacement, Comanche Peak staff wrote the specification for bids as the EPRI guidance document was being written, which enabled Luminant to incorporate many of the guidance elements. This specification and the requirements were then discussed at length with the suppliers.
Most of the suppliers took exceptions and increased the price, but this helped both the suppliers and Luminant to better understand the scope and effort and what was expected. It also resulted in detailed discussions and provided greater supplier clarity to each requirement. Comanche Peak is now in the preliminary design phase, and the EPRI document and checklist will be used to ensure requirements of each phase are addressed by the supplier.
For the video capture system, Luminant also has used the guidance document to ensure the integrity of the software and product. During the design review and factory acceptance testing (FAT), Luminant discovered supplier errors and a lack of understanding of third-party software products. This led to the FAT being repeated. Without a rigorous specification requirement, Comanche Peak would not have discovered the flaws at the factory, and these flaws could have resulted in an undesirable event upon installation.
Plenty to Gain
In short, vendors and nuclear plant owners who understand and address cybersecurity requirements up front will avoid costs on the back end. Benefits of using these EPRI documents include:
- Clearer security requirements: Bidders, suppliers, and licensees have a far better understanding of the cybersecurity requirements, because they are clearly specified.
- Lower costs: By significantly reducing misunderstandings that can lead to expensive scope changes, the EPRI documents help avoid costly rework.
- More-efficient work processes: Utility plant engineers know exactly which requirements are most relevant, alleviating confusion and saving time. In addition, engineers receive step-by-step guidance on how to implement cybersecurity controls throughout a critical digital asset’s life cycle.
- Enhanced safety and reliability: EPRI’s cybersecurity requirements provide better problem-detection and problem-solving capabilities, leading to safer, more reliable power generation. ■
— Matt Gibson ([email protected]) is senior technical leader at EPRI, and Jay Amin ([email protected]) is cybersecurity and digital program manager at Luminant.