In the information technology world, open-source platforms and software, as an alternative to proprietary ones, have long been commonly accepted. In process controls, not so much. That could be changing…
In the information technology world, open-source platforms and software, as an alternative to proprietary ones, have long been commonly accepted. In process controls, not so much. That could be changing…
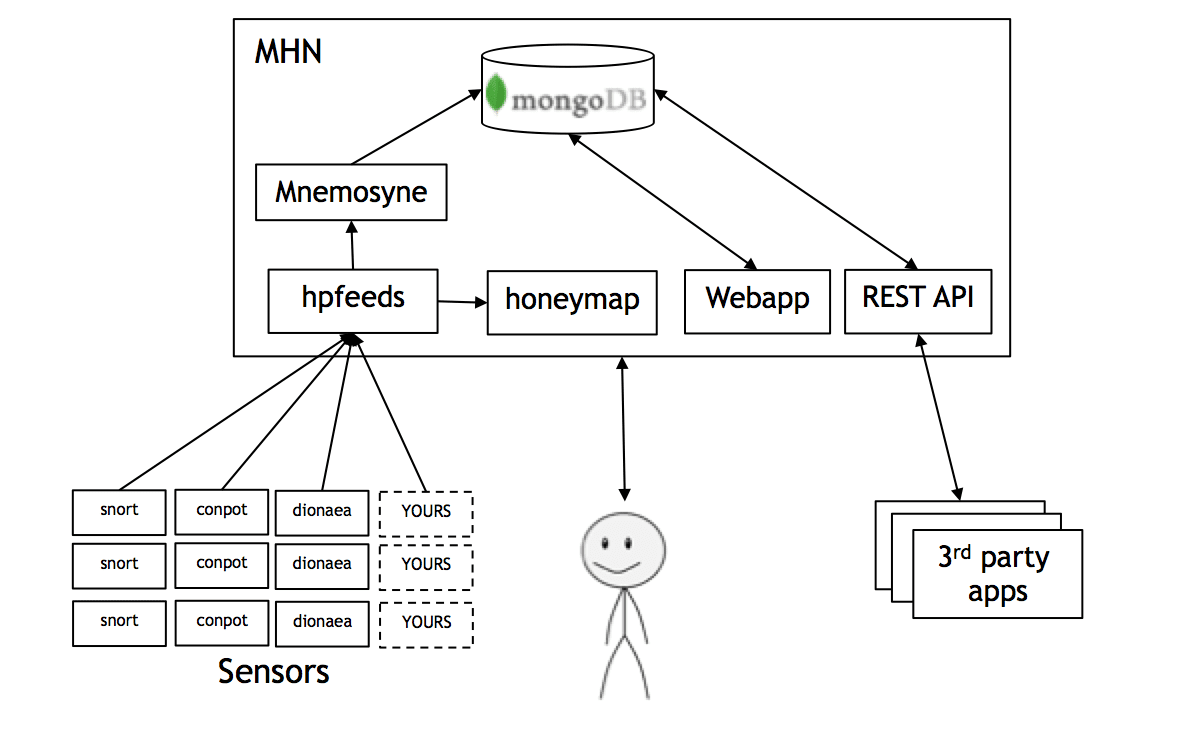
Cybersecurity threats facing the power industry have escalated dramatically in the past few years, as state-sponsored, organized crime, and hacktivist groups all seek to infiltrate U.S. energy infrastructure for cyber-espionage…

Even if your generating facility was exempt from previous versions of NERC’s Critical Infrastructure Protection standards, the latest version dramatically steps up the number of facilities encompassed, so the odds…

The latest version of Critical Infrastructure Protection standards applies to different facilities and assets than previous versions, so the first, critical step in compliance is to determine which facilities and…
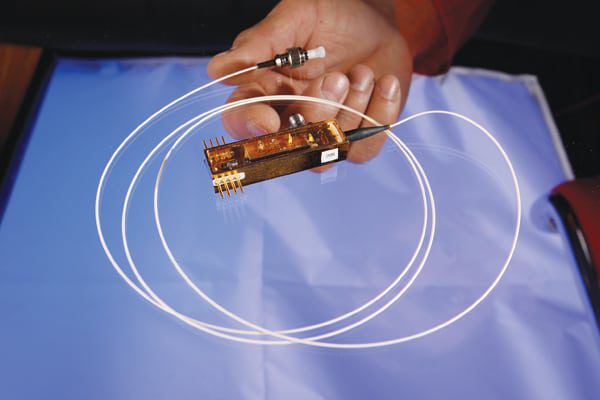
What if you could send a control message between two points on the electricity grid—say between a control room operator and a turbine or between a system operator and a…

When most people think of the AURORA cybersecurity threat today, they recall an image of an out-of-control generator during a 2007 demonstration test. But the threat didn’t end in 2007.…
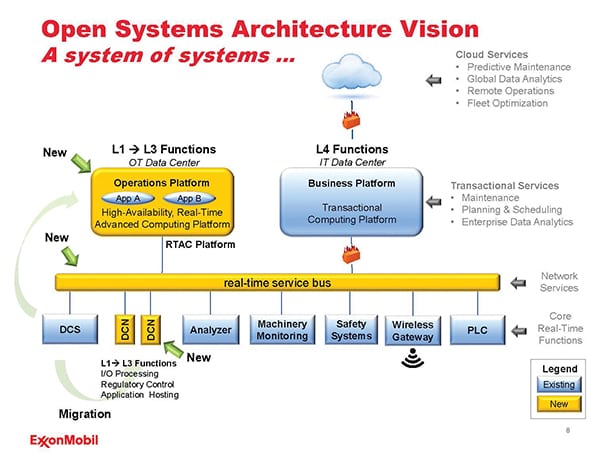
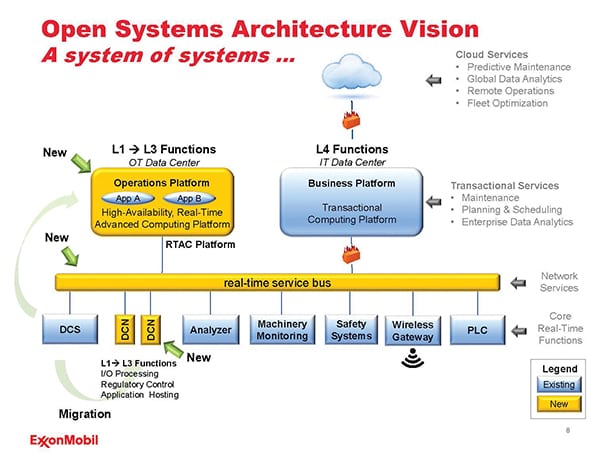
A recently published standard has been adopted globally to address risks arising from the use of business information technology (IT) cybersecurity solutions to address industrial automation and control systems (IACS)…