A bill to protect the U.S. power grid from cyber-attacks reintroduced by members of the U.S. Senate Intelligence Committee urges a “retro” approach to cybersecurity using a novel analog “disrupter” technology to guard computer-connected operating systems.
U.S. Senators Jim Risch (R-Idaho) and Angus King (I-Maine) on January 10 renewed their support of the Securing Energy Infrastructure Act, a bill that examines solutions to defend the grid from “potentially catastrophic cyber-attacks.” Senators Mike Crapo (R-Idaho), Martin Heinrich (D-N.M.), and Susan Collins (R-Maine) cosponsored the measure that was originally introduced in June 2016.
The Senate Committee on Energy and Natural Resources’ Subcommittee on Energy held a hearing on the bill on July 12, 2016, but no action on it was taken thereafter.
Holes in Digital Software Systems
The bill seeks to remove vulnerabilities that could allow hackers to access the grid through “holes in digital software systems,” the lawmakers said. Approaches to replace automated systems with “low-redundancies”—such as manual procedures controlled by human operators—could “thwart even the most sophisticated cyber-adversaries who, if they are intent on accessing the grid, would have to actually physically touch the equipment, thereby making cyber-attacks much more difficult,” they added.
Specifically, the bill seeks to establish a two-year pilot program within the Energy Department’s national laboratories to study and identify new classes of security vulnerabilities. It also calls for research on analog devices that could be used to isolate critical systems from cyber attacks.
Under the legislation, a working group would then be established to evaluate the technology solutions resulting from the pilot program. The working group—comprising federal agencies, the energy industry, state or regional agencies, and the national labs—would be tasked with developing “a national cyber-informed strategy to isolate the energy grid from attacks.” The energy secretary would then submit a report to Congress.
An Imminent Threat to National Security
The measure comes as the Department of Energy warned in its second installment of the Quadrennial Energy Review that the U.S. grid faces “imminent danger from cyber attacks.”
Last December, the U.S. and Canada released a joint strategy to thwart the growing threat of cyberattacks on the grid by strengthening the security and resilience of their shared grid infrastructure.
This heightened alarm about the electric grid’s vulnerability to cyber incidents is arising alongside revelations of Russian efforts to influence the 2016 U.S. presidential election, as detailed in a January 6–released analytic assessment that was drafted by the Central Intelligence Agency, the Federal Bureau of Investigation (FBI), and the National Security Agency. On December 29, the Department of Homeland Security (DHS) and the FBI issued a joint analysis report that outlines technical details regarding tools and infrastructure used by the Russian civilian and military intelligence services to attack critical infrastructure networks in foreign countries.
But the power sector has been on alert for years, owing to a growing number of notable cyber incidents. On December 23, 2015, a number of energy companies in Ukraine were targeted, and a swathe of unscheduled power outages afflicting three regional power distribution companies prompted a blackout affecting 225,000 Ukrainians. A U.S. interagency team in February 2016 confirmed that that incident—pegged as the first time that malware had apparently been used to prompt a large-scale blackout—was conducted by “external malicious actors,” though it did not directly implicate a specific entity for the attacks.
On December 18, 2016—nearly a year after that attack—a cyber attack on Kiev’s power grid resulted in another power outage amounting to 200 MW of capacity, as an executive of Ukrenergo, a Ukrainian state-run power distributor, told Reuters.
Calling for “Disrupters”
According to Senator Risch, the bill’s concept to use “retro” technology to thwart cyberattacks was inspired by the 2015 Ukrainian incident. “The attack could have been worse if not for the fact that Ukraine relies on manual technology to operate its grid,” a statement from his office said. “The legislation seeks to build on this concept by studying ways to strategically use ‘retro’ technology to isolate the grid’s most important control systems.”
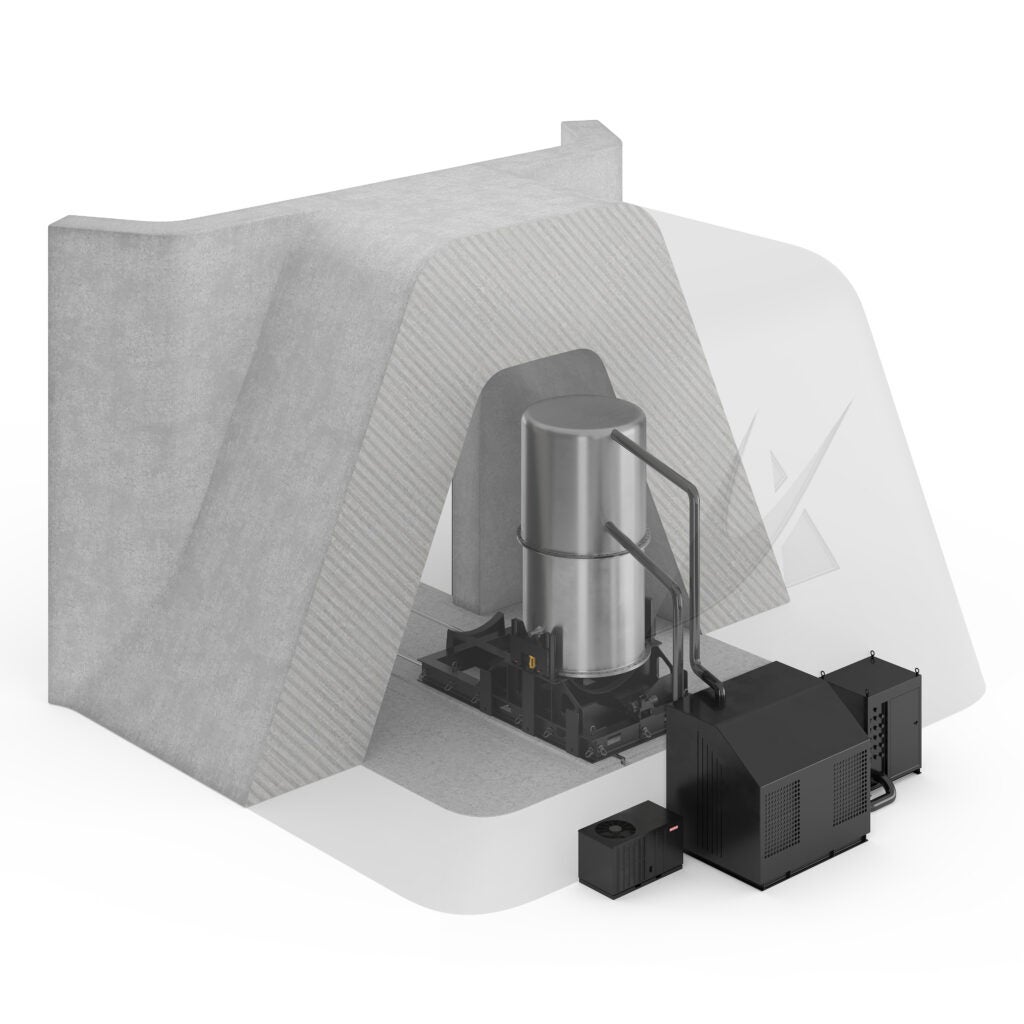
The bill doesn’t pinpoint a specific technology. However, according to Idaho National Laboratory (INL) spokesperson Misty Benjamin, the technology referenced in the bill is a “disrupter.”
This type of technology provides a physical limitation or system barrier to interrupt a cyberattack, she told POWER on January 13. Among other things, it would likely involve insertion of an analog attack surface disruption zone that disrupts a remote cyberattack, requiring the attacker to physically access the asset to have an effect. “The disruption zones are based on the fundamental science and physics of the system being controlled, thus tailored specifically to the critical system,” Benjamin said.
Benjamin added that INL is investigating a broad range of new solutions that “systematically re-engineer” critical functions to disrupt critical effects of cyber attacks. “These engineered physical devices simplify the layers of complexity (operating systems, networks, application software) on the most critical functions, limit the digital discovery of their presence, and provide fundamental protections that permit broader innovations on the cyber portions of the larger system.”
Sen. Risch in September 2016 met with officials from the Department of Homeland Security and INL to discuss the “new technology” that his office said would help protect the grid.
Robert M. Lee, CEO and founder of industrial cybersecurity firm Dragos, Inc., who was involved in the U.S. government’s investigation of the Ukraine attack, told POWER on January 13 that a lot of the push in this area stems from Tim Roxey, Michael Assante, and Andy Bochman, who wrote a paper titled “The Case for Simplicity in Energy Infrastructure.”
“The idea, which I fully support,” Lee said, “is to ensure we are not putting more code, programs, and complexity into sensitive portions of our infrastructure than are required for the business. Simply put, we do not want to have more attack surface for attackers to take advantage of than is required. The idea of out-of-band and analog systems to help prevent certain types of attacks such as the Aurora-styled attack is an excellent idea.”
“However,” he said, “there will always be the need for cybersecurity programs, technologies, and investments to help defend against other styles of attacks, such as the use of the infrastructure systems against themselves, as we saw in the 2015 Ukraine power grid attack. Folks should not view this as a silver bullet solution to prevent cyber attacks but instead should view this approach as one more tool in the toolbox to help reduce risk against cyber threats.”
A Return to Analog Is Complicated
However, as Rob Manning, vice president of transmission for the Electric Power Research Institute’s (EPRI’s) Power Delivery and Utilization research sector, pointed out in an interview with POWER on January 11, a return to analog in the U.S. grid could prove highly problematic.
“Today’s grid is far more complex than the days when analog control devices on the grid were dominant. And to think that we could create a cyber block, say, by inserting analog devices, it sounds very challenging to me,” he said. “In fact, I don’t know how we would do it. You certainly have to spend some time and thought studying it because without a doubt, the insertion of analog devices would have unintended consequences.”
Manning noted that today’s grid is much different that it was when analog devices were controlling it. New technology has enhanced grid reliability considerably, allowing for new roles, such as for renewables integration and demand response. “All of those would be compromised in some way” he said.
—Sonal Patel, associate editor, and Gail Reitenbach, editor (@POWERmagazine, @sonalcpatel, @GailReit)
Updated (January 13): Adds details from the Idaho National Laboratory; adds comments from Robert M. Lee, CEO and founder of industrial cybersecurity firm Dragos, Inc.