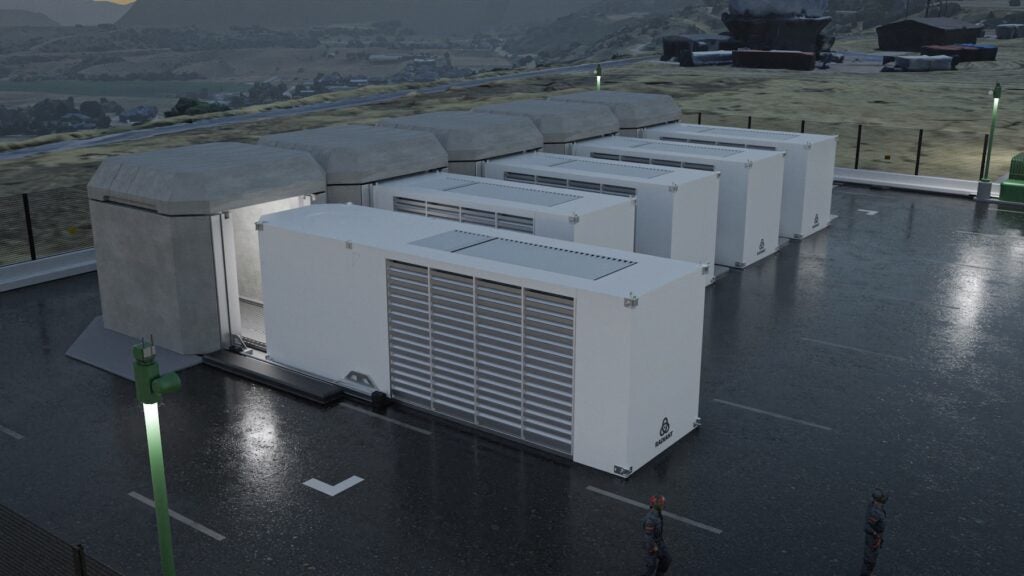
Computers at Iran’s Bushehr nuclear reactor and around the country have reportedly been infected by the Stuxnet worm, a sophisticated malware that attacks supervisory control and data acquisition (SCADA) systems at power plants, factories, and military installations.
Iranian officials admitted on Saturday that the worm had infected at least 30,000 computers in the country but said on Sunday that none of the nuclear reactor’s crucial control systems were affected, Computerworld reported on Monday.
The First Cyber Attack Specifically Targeting Control Systems
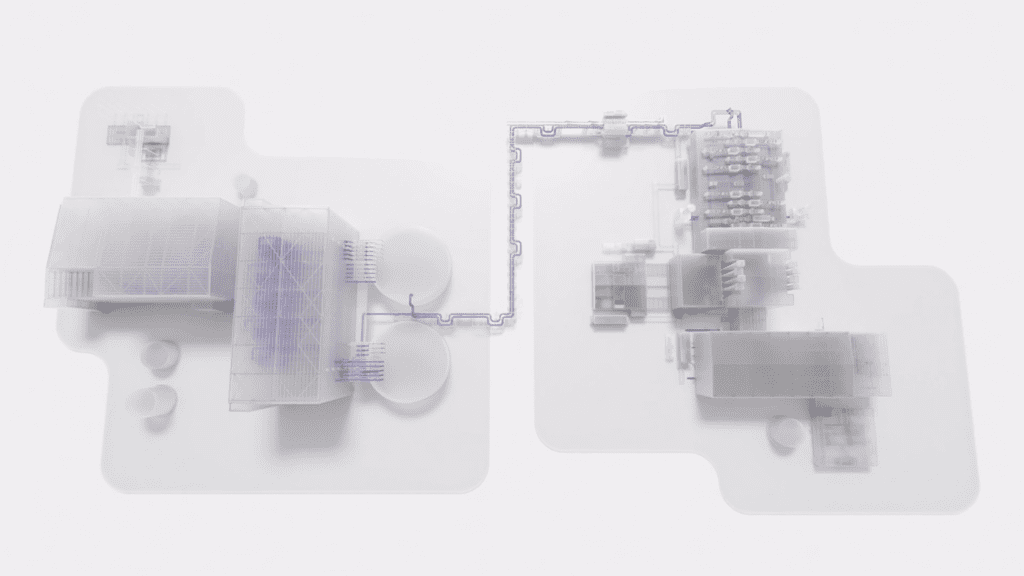
According to antivirus company Symantec Corp., Stuxnet looks for industrial control systems and then changes the code in them to allow the attackers to usurp controls of industrial equipment such as sensors, actuators, pumps, and valves without the operators knowing. “In other words, this threat is designed to allow hackers to manipulate real-world equipment, which makes it very dangerous,” the company said on its website.
“Stuxnet searches for industrial control systems, often generically (but incorrectly) known as SCADA systems, and if it finds these systems on the compromised computer, it attempts to steal code and design projects,” Symantec explained. “It may also take advantage of the programming software interface to also upload its own code to the Programmable Logic Controllers (PLC), which are ‘mini-computers’, in an industrial control system that is typically monitored by SCADA systems.”
Symantec said that motives for the malware’s creation—which could have involved five to 10 people over six months—were unclear, but industrial espionage was probably one of them.
“It’s like nothing we’ve seen before—both in what it does, and how it came to exist. It is the first computer virus to be able to wreak havoc in the physical world,” the company added. “It is sophisticated, well-funded, and there are not many groups that could pull this kind of threat off. It is also the first cyber attack we’ve seen specifically targeting industrial control systems.”
The worm, discovered in July this year (but which has existed since January 2010, according to Computerworld), is said to have targeted mainly Iran, Indonesia, and India. Symantec estimates that Iran has incurred almost 59% of hits by the worm, followed by Indonesia (18.2%), India (8.31%), and Azerbaijan (2.57%). The U.S. incurred about 1.56% of hits, the company said.
Worst Case Scenarios
Industry analysts project that compromised SCADA systems could result in a variety of worst-case scenarios ranging from stolen data to causing systems such as cooling pumps to malfunction.
Discussions within the industry have surmised that there are several fixes and workarounds to the worm. Panelists at an August webinar hosted by critical infrastructure reliability group Industrial Defender asserted that standard Internet security scanners (such as Norton, Symantec, etc.) can find Stuxnet on USB drives and protect control systems.
“By now all antivirus vendors have issued signatures to detect the .LNK file exploit the worm uses to propagate, and most have signatures for the known versions of Stuxnet worm itself,” the group said. “However, you will only be able to take advantage of those new signatures if you are keeping your [antivirus] signatures up to date.”
However, Andrew Ginter, chief security officer at Industrial Defender, in a recent blog refused to downplay the malware’s potential effects. “Stuxnet is the biggest thing to hit industrial control system security since Maroochy,” he said, referring to the April 2000 case in which 49-year-old Vitek Boden used a stolen wireless radio, a SCADA controller, and control software to release up to one million liters of sewage into the river and coastal waters of Maroochy Shire in Queensland, Australia.
But Ginter also lambasted media suggestions that the worm was developed specifically to target the Iranian nuclear reactor, calling the reports “nonsense.”
“What control systems security experts agree on, is that the intent behind Stuxnet was sabotage. Beyond this, there is only speculation,” he said. “There is no compelling evidence a nation-state military authored the worm. There is no compelling evidence the Iranian reactor or Iranian uranium processing facilities were the target of the worm. This is all speculation based on circumstantial evidence.”
Sources: Computerworld, Symantec, Industrial Defender, The Age