|
|
|
|
|
| Sponsored Content |
|
For security leaders, what are implementation challenges for ransomware measures in ICS/OT? Discover the keys to implementation according to the characteristics of ICS/OT systems and processes.
Trend Micro, a global cybersecurity leader, helps make the world safe for exchanging digital information. Fueled by decades of security expertise, global threat research, and continuous innovation, our cybersecurity platform protects hundreds of thousands of organizations and millions of individuals across clouds, networks, devices, and endpoints.
|
|
 |
|
|
|
| Sponsored Content |
|
Companies have used the PI System to track minute-by-minute performance and compare metrics to saved data histories for years at the plant level. Now many need to track efficiencies across multiple facilities with diverse power generation methods but getting the right data across plants is tough.
PI System centralization makes it easy to access the right data for full visibility across your power generation portfolio and can save thousands in analysis, integration, and licensing costs.
Learn how to get started centralizing your PI System data:
- The benefits of a centralized PI System.
- The challenges for implementing data centralization.
- Steps for planning an effective centralization project.
- Profiles of four unique centralization projects.
Download the White Paper NOW!
|
|
 |
|
|
|
|
|
 |
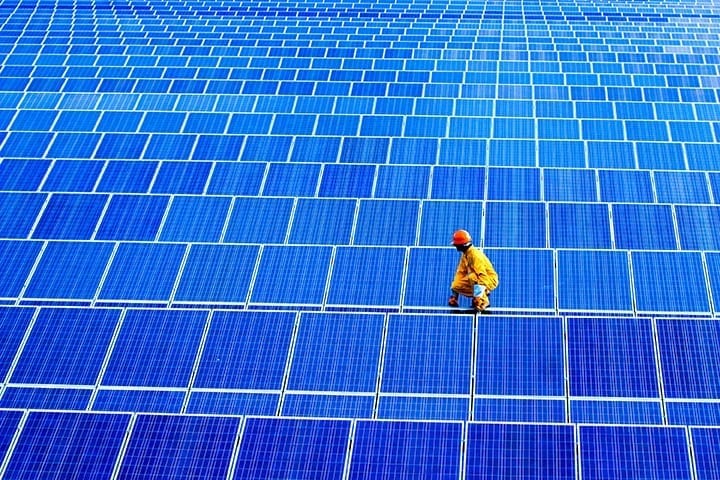
Zinc Batteries Power Stationary Energy Storage
As solar, wind and other renewable resources play a larger role on the power grid, renewables’ essential partner—energy storage—must keep pace to provide power at peak hours when the sun… |
|
|
|
|
|
|
 |
Current POWER Magazine Issue
|
|
|
|
|
|
|
|